Overview
In this guide, we demonstrate the Slack integration with the RCDevs Identity Provider through SAML.
Refer to Slack documentation for SAML configuration on Slack.
IdP configuration on Slack
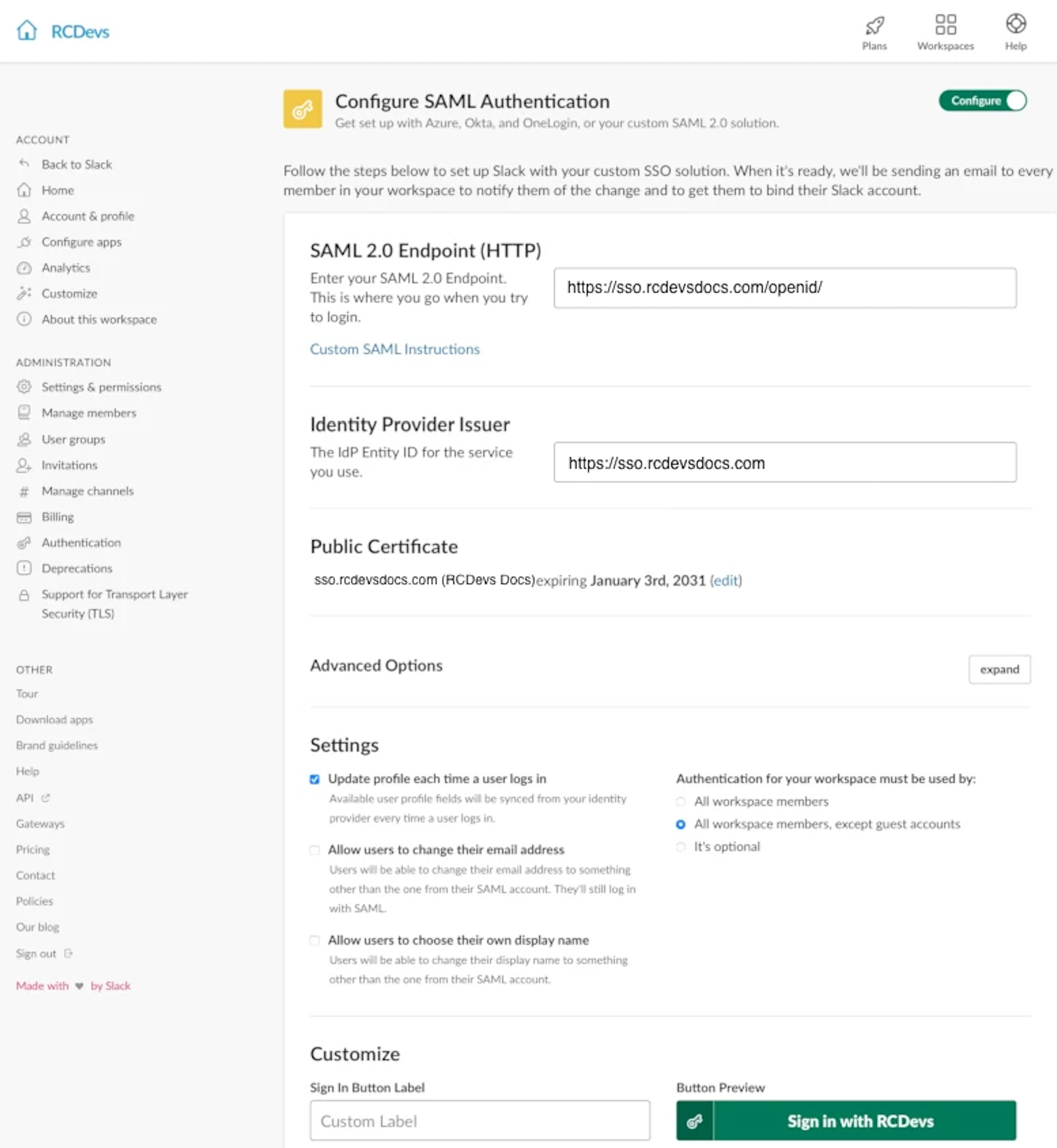
Login to the Slack web page with your Slack administrator account. In the Administration category, navigate to Authentication and configure your SAML authentication provider. On the SAML configuration page, you will find only a few settings to configure:
- SAML 2.0 Endpoint;
- Identity Provider Issuer
The provided information in the previous screen can be retrieved from your SAML metadata page. On my side, it is accessible through
https://sso.rcdevsdocs.com/ws/saml URL.
Providing the following output:
<EntityDescriptor xmlns="urn:oasis:names:tc:SAML:2.0:metadata" entityID="https://sso.rcdevsdocs.com">
<IDPSSODescriptor protocolSupportEnumeration="urn:oasis:names:tc:SAML:2.0:protocol">
<KeyDescriptor use="signing">
<KeyInfo xmlns="http://www.w3.org/2000/09/xmldsig#">
<X509Data>
<X509Certificate>MIIGfzCCBGegAwIBAgIRAM9/TyvDiZAahDgzYkWGRdIwDQYJKoZIhvcNAQELBQAwUjEXMBUGA1UEAwwOUkNEZXZzIERvY3MgQ0ExCzAJBgNVBAsMAkNBMR0wGwYDVQQKDBRSQ0RldnMgRG9jdW1lbnRhdGlvbjELMAkGA1UEBhMCTFUwHhcNMjQwNzE1MTM0OTA3WhcNMzQwNzEzMTM0OTA3WjBgMRswGQYDVQQDDBJXZWJBRE0gQ2VydGlmaWNhdGUxDzANBgNVBA0MBlNFUlZFUjEXMBUGA1UECgwOUkNEZXZzIFN1cHBvcnQxFzAVBgNVBGEMDlZBVExVLTAwMDAwMDAwMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEA1w3PR1Q+78jdD12g4Di3ljcthoZwvpQuwmuOm/+fBthQjrHR1UIY3HDkulCOYpBRiNNj6ED49eyF9jIeO/zVO5QXnzX4gmasZPd06ZYAD8pkDc7fnnxZD4aSHDKQcF1xwUnHESUCPzWR1Wy3t6ifwl85uRuC+QlskMv4t82LqeMQeSBdeBqNpADm9Hmg8AO5BK4Oz/NNooB46P5RYDEerY1D/qOfLkuzEDr2C2Z1rGvtG7+7EpaS+b9Ipnz/fT71QACPxJym98YWEp/1Fb/clC6QLKQuQ+AzheTVZyyeOhOYFxsoGEu+wDFAERXWWAr5sPnayDJiZdXbH+712ri35y9oFWOxZC1diATOS/MRc05bAzgAbyiQe1PrhDfwRiL4YF0EtLvuZJGBH031DZS3THdYSeONDhsImbNYFYLPpzRqb5iXssN+KBPAdCfYJ2IMfjAV4li0s1WSC40iZ5MAkwovE0HD++DVO2HHBJ9hYl6aqa35lGm/QSjkUYvw2xX3kvc3utPQcqUkYDWzF7tLIMpTzO6FtD1pR/FR6DKkqmx9NhLMdIi9eNGK4MG+MgKwCXhE1I6aJxVoRCbAihb0wgnR+Y38P4bJUYzvDCC4upE3DLc+ct5VJ/rtCo9UDyVQGsLDD9cDoywdr6feM/Pou+LpccVNAHul1FJ9CPKxyVECAwEAAaOCAUAwggE8MAsGA1UdDwQEAwIF4DATBgNVHSUEDDAKBggrBgEFBQcDATCBygYIKwYBBQUHAQEEgb0wgbowJgYIKwYBBQUHMAGGGmh0dHA6Ly8xOTIuMTY4LjQuMTYwL29jc3AvMCYGCCsGAQUFBzABhhpodHRwOi8vMTkyLjE2OC40LjE2MS9vY3NwLzAzBggrBgEFBQcwAoYnaHR0cDovLzE5Mi4xNjguNC4xNjAvY2FjZXJ0Lz9mb3JtYXQ9ZGVyMDMGCCsGAQUFBzAChidodHRwOi8vMTkyLjE2OC40LjE2MS9jYWNlcnQvP2Zvcm1hdD1kZXIwSwYDVR0fBEQwQjAfoB2gG4YZaHR0cDovLzE5Mi4xNjguNC4xNjAvY3JsLzAfoB2gG4YZaHR0cDovLzE5Mi4xNjguNC4xNjEvY3JsLzANBgkqhkiG9w0BAQsFAAOCAgEACy/zl7IPSaOn2wEZ66xQNxm9FW408jMrQS2Y6hFvfzRMNhbOh+ZwNFSgCijUJ4ASZVQeZIiYN8f/quH80Y7AJE3kcTpXvJE2LozDbUMsXe0GpkNuzDojbp3K2ZcgUitL0q/rDHPBXXExl1AEhPgpwN1I7ZyHPfZpU92XxcsoSrUi8AMmzoVwlna30RMkkCDDBsf+an1uxdrdwMQLeQddOFddAUI80NWvh0drnv1epkT34K+RpvEAU514a3suErDMIqp+h7BqTdPrdiRkIhTutgSsPquhGIDzv+WvGBzFGWPAfudQHE5jMn3lPgN3r75HrdNfMkVEv0jclpp3VhiUnwQzNQn2UzVe7LQh8ixjEg1kwtIQ8UuwX6LOZ7a51WuKkRfS1iw1yDCM1UmGNuoMGqI6bxwFbBZ1C3brgJKjXBciEpXrSpcJ+ulhDYYUrCmGnpg6xyJ6veWfT2tVExLcffv4edT0KCJuKsyTztLFtT9A9ihyV/lPBsVUtIipe2CaCXupP84812s0cgo6XkcAr99pvtPNLZg9aBLuVt7GmyJSQeLJ6z+QWlkKnsEh7HlSrV2RC/wsTYlTeTRZFmiNa1RGx4UsNyTf9Igp+EG4Nh/UBhGO1Jkn1dIRZyb/qgcF/DWCSdbwFIKxuaKA12KFJMFS4aMV1e0QLDhLfpZ1/10=</X509Certificate>
<!-- Cert Fingerprint (SHA1): 32774463a2e892150f46852b3fdcac7f5be924dc -->
<!-- Cert Fingerprint (SHA256): e0bd10584f5c3a554e279b9241619e8fdf9c3bfbe95c90da939f0342546e52ac -->
<!-- Cert Fingerprint (MD5): 639ed5b4241047c8382f897fc459a714 -->
</X509Data>
</KeyInfo>
</KeyDescriptor>
<SingleLogoutService Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-Redirect" Location="https://sso.rcdevsdocs.com/openid/index.php"/>
<SingleLogoutService Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-POST" Location="https://sso.rcdevsdocs.com/openid/index.php"/>
<SingleSignOnService Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-Redirect" Location="https://sso.rcdevsdocs.com/openid/index.php"/>
<SingleSignOnService Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-POST" Location="https://sso.rcdevsdocs.com/openid/index.php"/>
</IDPSSODescriptor>
</EntityDescriptor>
In the Advanced options section, click on Expand and configure Slack issuer which will be sent to your IdP:
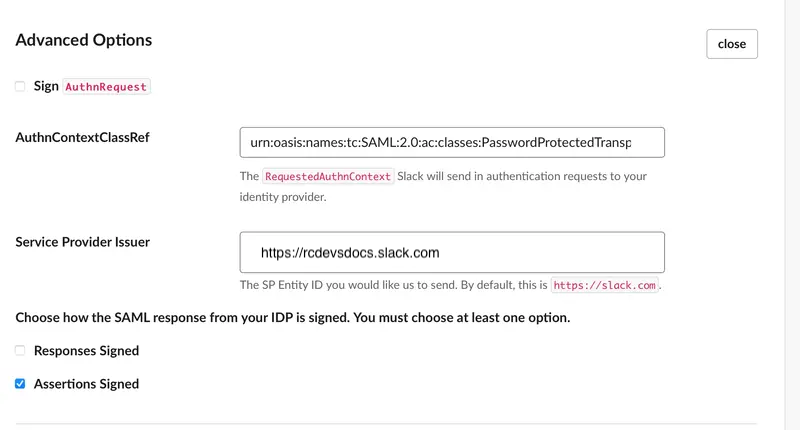
In the same section, you can enable the following:
- Sign AuthnRequest;
- Responses Signed;
- Assertions Signed.
The 3 modes are supported with RCDevs IdP.
In that example, we just enabled the Assertions Signed option which is the default mode of the RCDevs IdP.
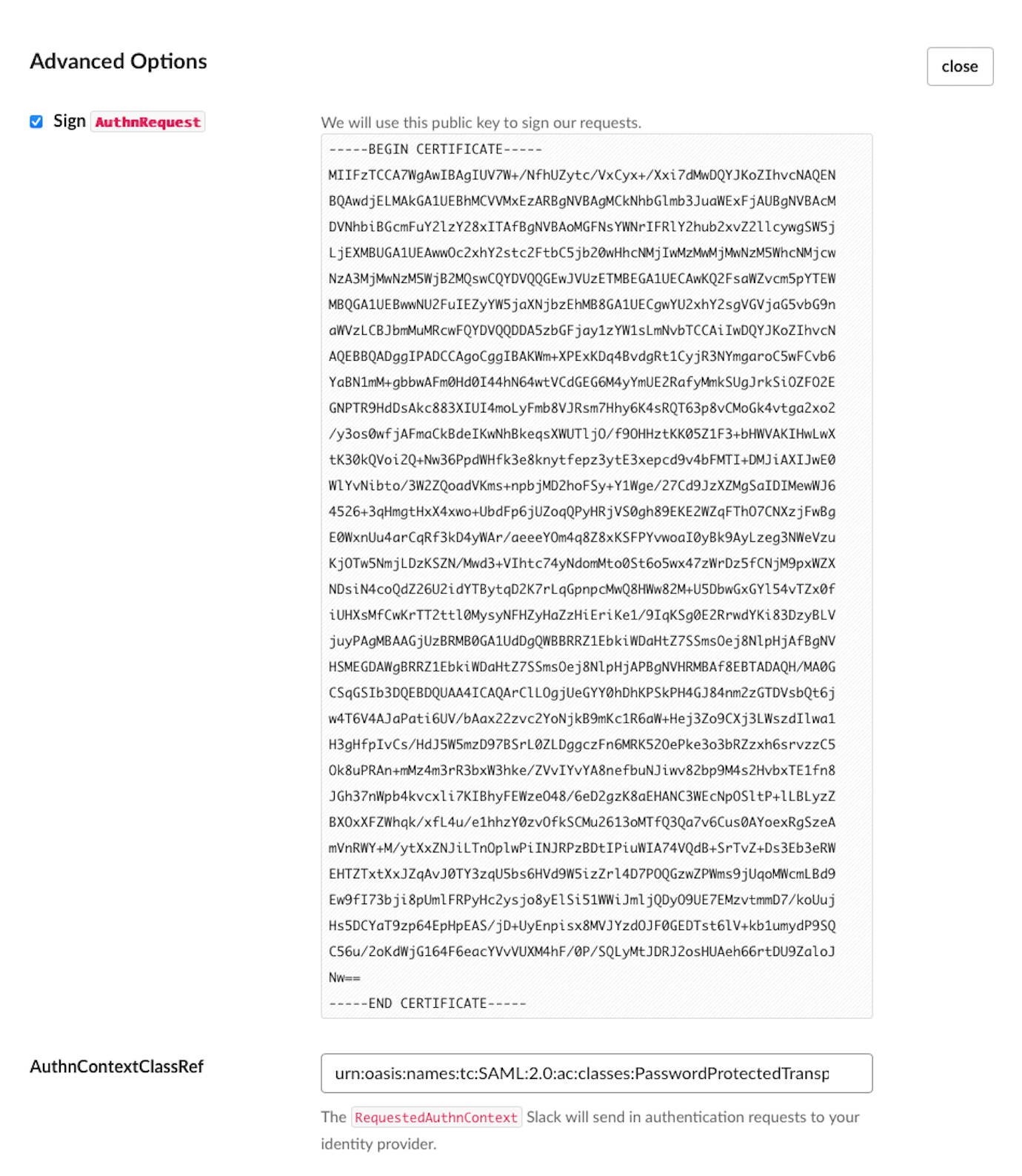
If you enable the Sign AuthnRequest setting, you will see the certificate used by Slack to sign the request. Copy the content of that certificate, as you will need to configure it later in your Client Policy.
Slack Configuration on the IdP (Client Policy)
The Slack configuration on the IdP simply consists of creating a client policy.
Let's create a Client Policy for Slack. Login on WebADM Administrator portal, click on Admin tab, click on Client Policies and then Add Client button. Name your client policy and optionally provide a description.
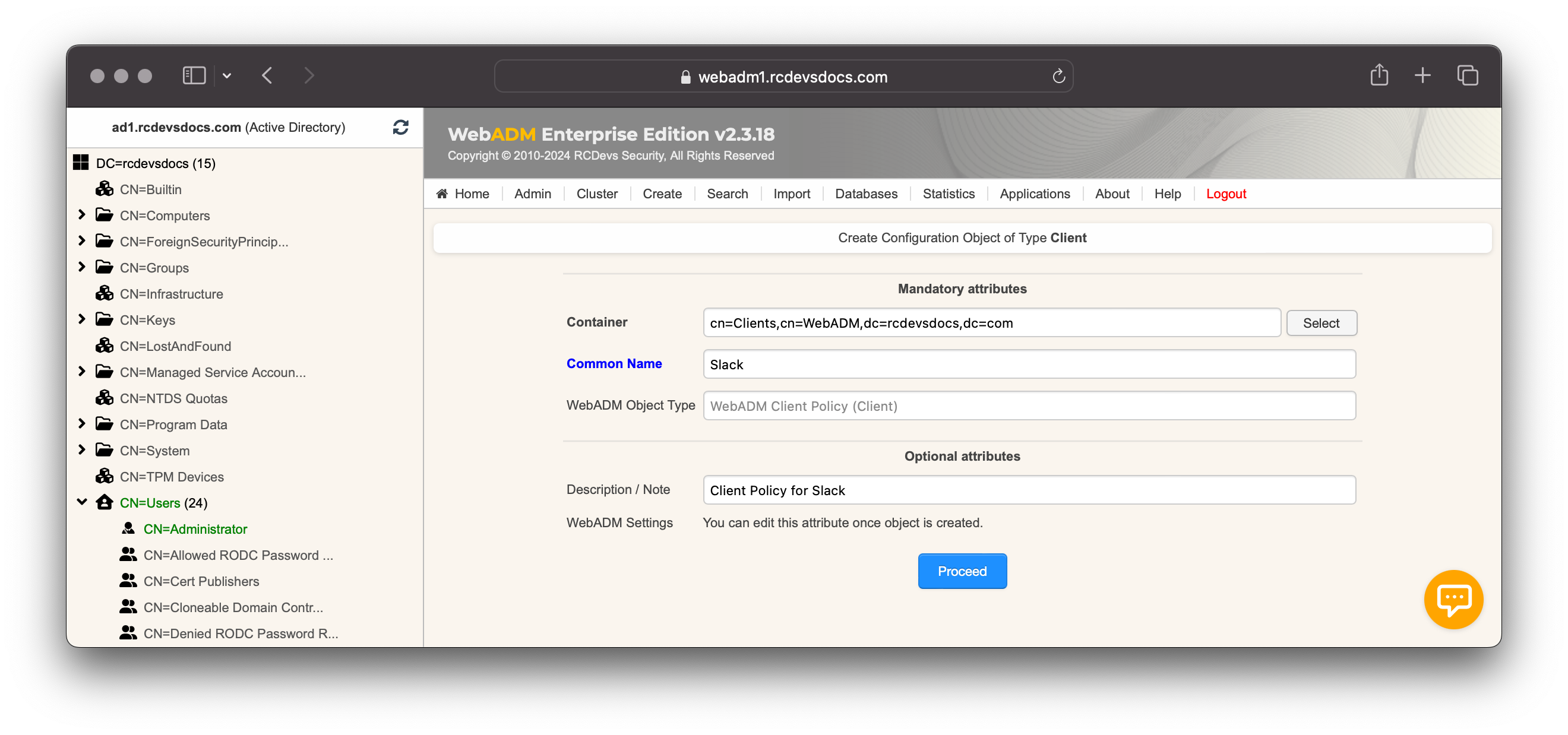
Click Proceed followed by Create Object.
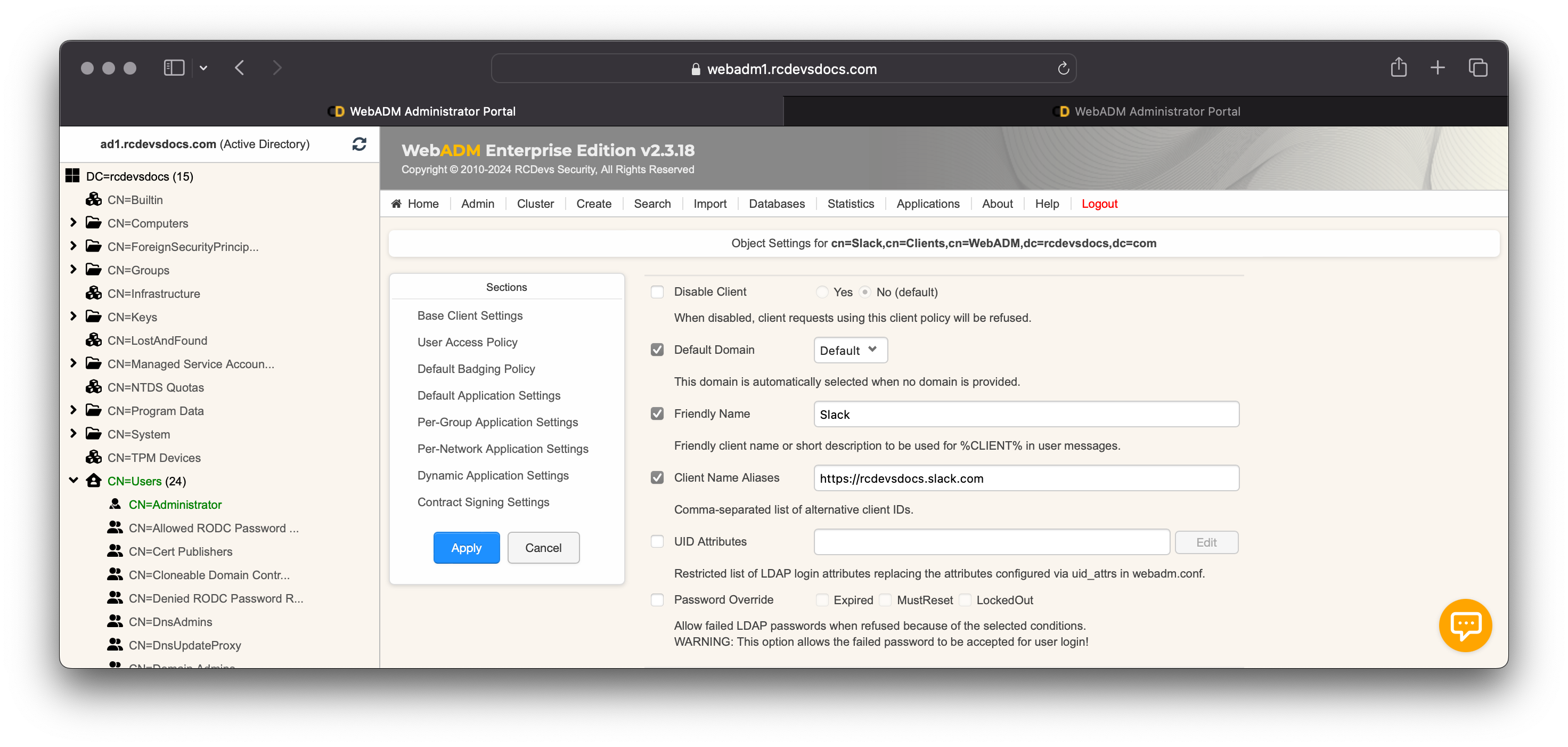
You are now entering the policy configurator. Configure the Default Domain, a Friendly Name (optional), and set the Client Name Aliases.
Configure the AssertionConsumerServiceURL as the Client Name Aliases in your Client policy to facilitate the matching process.
On my side, it is https://rcdevsdocs.slack.com.
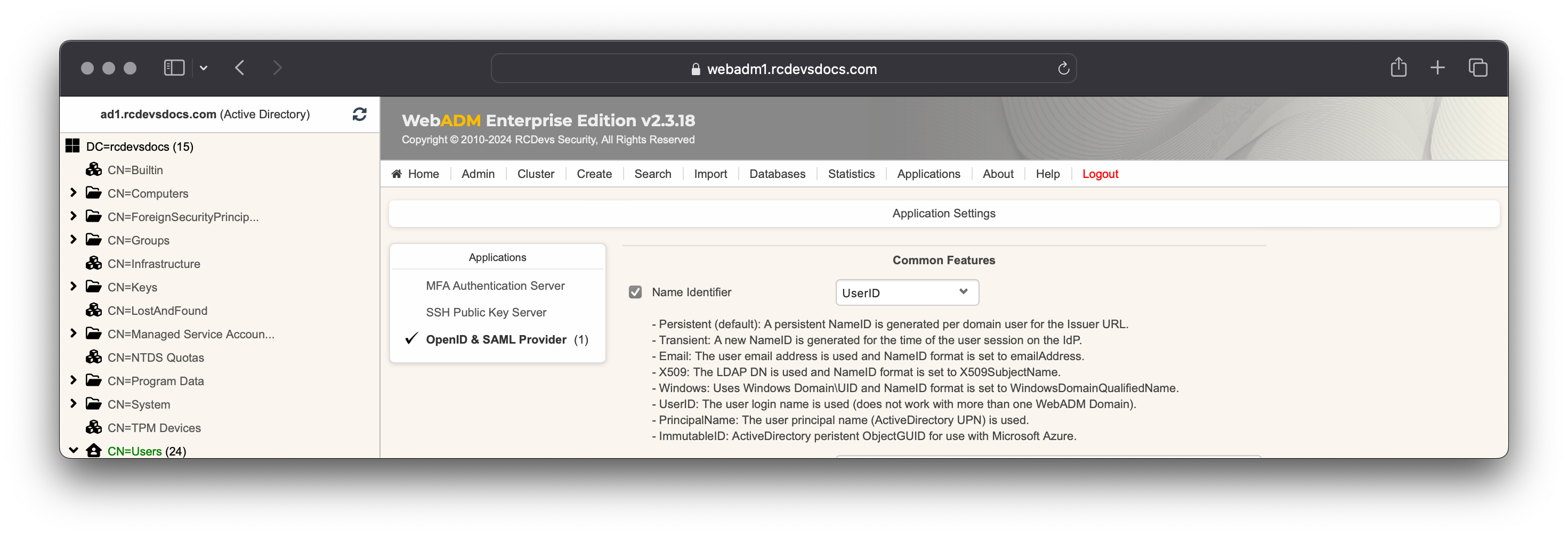
Scroll down to Default Application Settings, click on the Enforced Settings checkbox and click Edit button. In Applications box, select OpenID & SAML Provider.
In the Common Features section, set the Name Identifier setting to UserID:
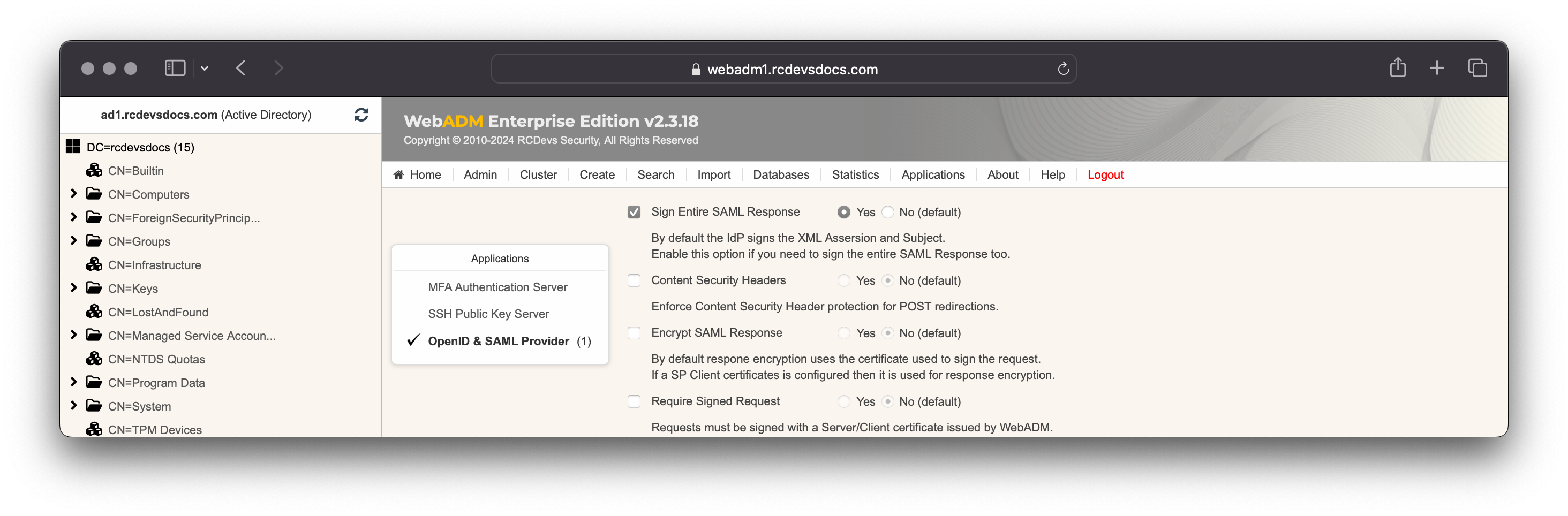
If on Slack, in Advanced Options you configured Responses Signed then you must configure it in your Slack Client Policy:
If you enabled Sign AuthnRequest in Slack configuration, then you have to configure 2 more settings in your client policy:
- Require Signed Request;
- The client certificate used by Slack
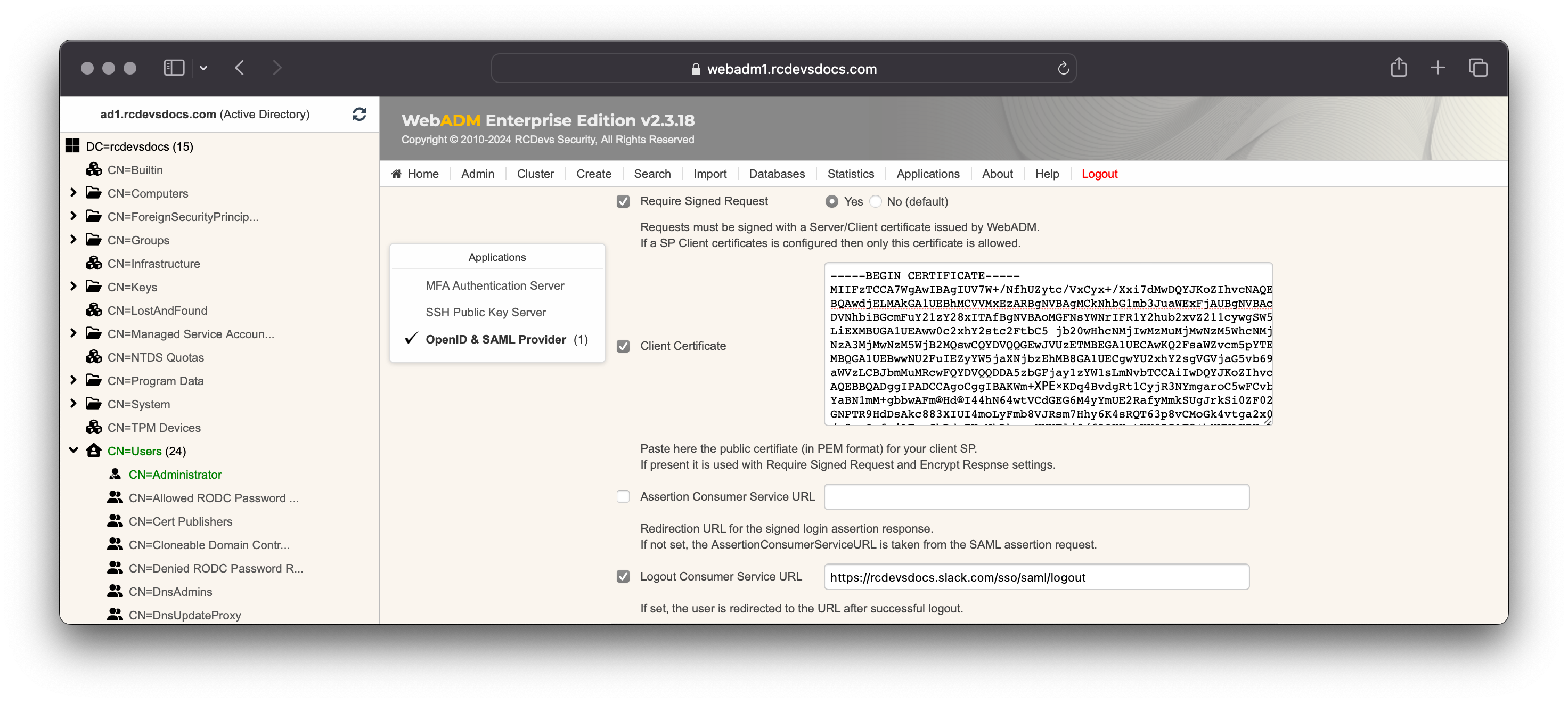
Note that when the client certificate used by Slack expires, it will be renewed by the Slack team. You will need to update it in your client policy; otherwise, the authentication requests sent by Slack to the IdP will be refused by the IdP.
You can optionally configure the Logout Consumer Service URL setting to inform the SP of logout actions on the IdP.
You can also configure authentication settings by accessing the MFA Authentication server in Applications box.
Scroll down and click Apply to apply the IdP configuration for Slack.
On the next page, click Apply so save your client policy.
That's it! Configuration is done, you can try to perform a login.
