Overview & Concepts
Building a Unified IAM Infrastructure
In large organizations, consolidating Identity and Access Management (IAM) systems from different vendors across various locations is a daunting and often impractical task. This is especially challenging for corporate groups and companies that frequently acquire new subsidiaries, resulting in fragmented information systems. Consolidation projects are typically long, costly, and rarely yield the expected results, leaving behind a mix of well-integrated systems and legacy systems that still need to function.
RCDevs addresses these challenges by offering a federated approach to IAM and Identity Provider (IdP) management. The RCDevs solution federates multiple IAM systems, integrating them into a cohesive meta-IAM platform. This top-level meta-IAM provides a unified view of all the underlying IAM systems, allowing seamless integration with cloud or on-premises services like email, VPNs, and OpenID Connect (OIDC). With this approach, there's no need for complex IdP cascading or password management, simplifying the IAM consolidation process.
For example, consider a corporate group, MyCorp, which has acquired two companies—one using Okta and the other using local Active Directory (AD) systems—while MyCorp itself uses Entra ID. RCDevs creates a meta-IAM that aggregates these disparate systems into a unified platform. This enables cross-IAM application access policies, unified UPN naming conventions, and centralized IdP services across the entire organization.
WebADM and External IAM Integration
With WebADM version 2.3.20 and beyond, RCDevs introduced native integration capabilities for external IAM providers, allowing organizations to synchronize accounts and groups from their cloud IAM platforms into WebADM’s LDAP tree. This synchronization was initially one-way—from the external IAM provider to WebADM—preserving group memberships and enabling external identities to be added to locally defined groups.
Starting with version 2.4.4-4, WebADM takes this integration further by supporting bi-directional synchronization with major cloud IAM systems, including Entra ID, Okta, Duo, PingOne, OneLogin, and Google Workspace. This new two-way sync mode, configurable in the WebADM Domain settings, introduces real-time, seamless object management between WebADM and remote IAM systems.
Key enhancements include:
- Full support for creation, deletion, renaming, copying, moving, and attribute modification of users and groups across both local and remote IAMs
- Real-time synchronization of local object changes to remote systems
- Transparent object copy/move actions between IAM platforms (e.g., from Entra ID to Okta), mimicking native LDAP object management
- Retention of group structures and memberships during cross-service operations
- Support for marking synced users as temporary with auto-deletion on the next sync
- Ability to copy users along with their current passwords for streamlined onboarding
These capabilities provide true cross-system identity management, allowing WebADM to function not only as a centralized view of federated IAM systems but also as a central control point for multi-IAM object lifecycle management.
In scenarios like mergers and acquisitions, this bi-directional sync significantly reduces integration complexity and operational overhead, offering consistent security policies, centralized user lifecycle operations, and efficient group-based access control.
Conclusion
RCDevs and WebADM empower organizations to overcome the fragmentation and complexity of managing multiple IAM systems. With real-time, bi-directional integration and centralized object control, they provide a flexible, secure, and scalable foundation for unified identity management across any combination of on-premises and cloud IAM providers.
Actions/permissions required on EntraID
To perform operations such as locking a user account, checking or changing an Entra ID user's password, and retrieving user and group information using Entra ID APIs from WebADM, you'll need specific API permissions. These permissions must be granted through a registered application in Entra ID, and the application must have the appropriate permissions described later in this docuementation.
App Registration
From the EntraID portal, access the App Registration menu.
Click on the New Registration button to start the registration process. Provide a name to easily identify your application that will be used for WebADM framework purposes.
In this example, I named it WebADM Sync.
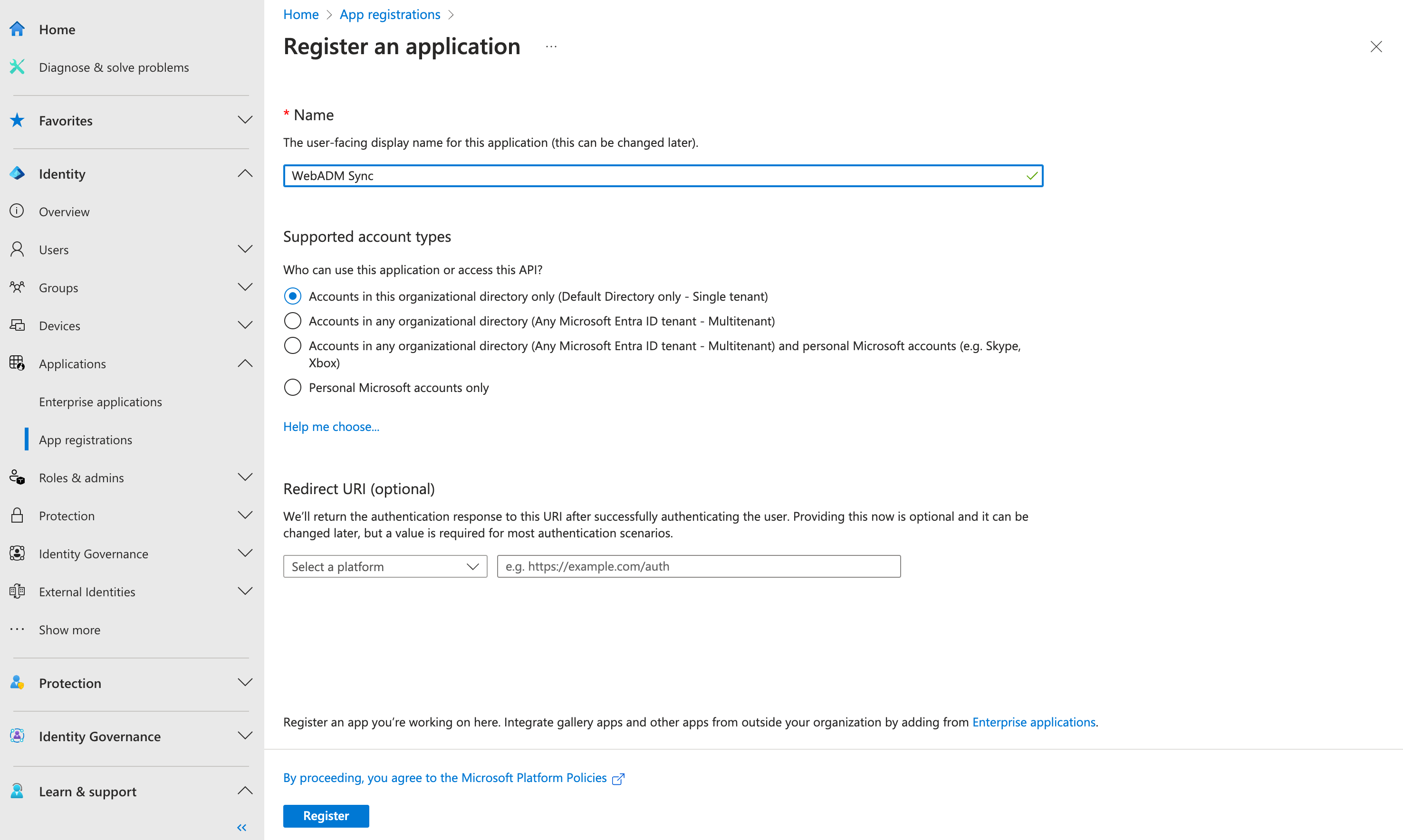
Click on the Register button, and you will be redirected to the registered application's overview menu.
From the overview menu, you will need the following information for the tenant/application configuration in the WebADM Framework:
- Application (client) ID
- Directory (tenant) ID
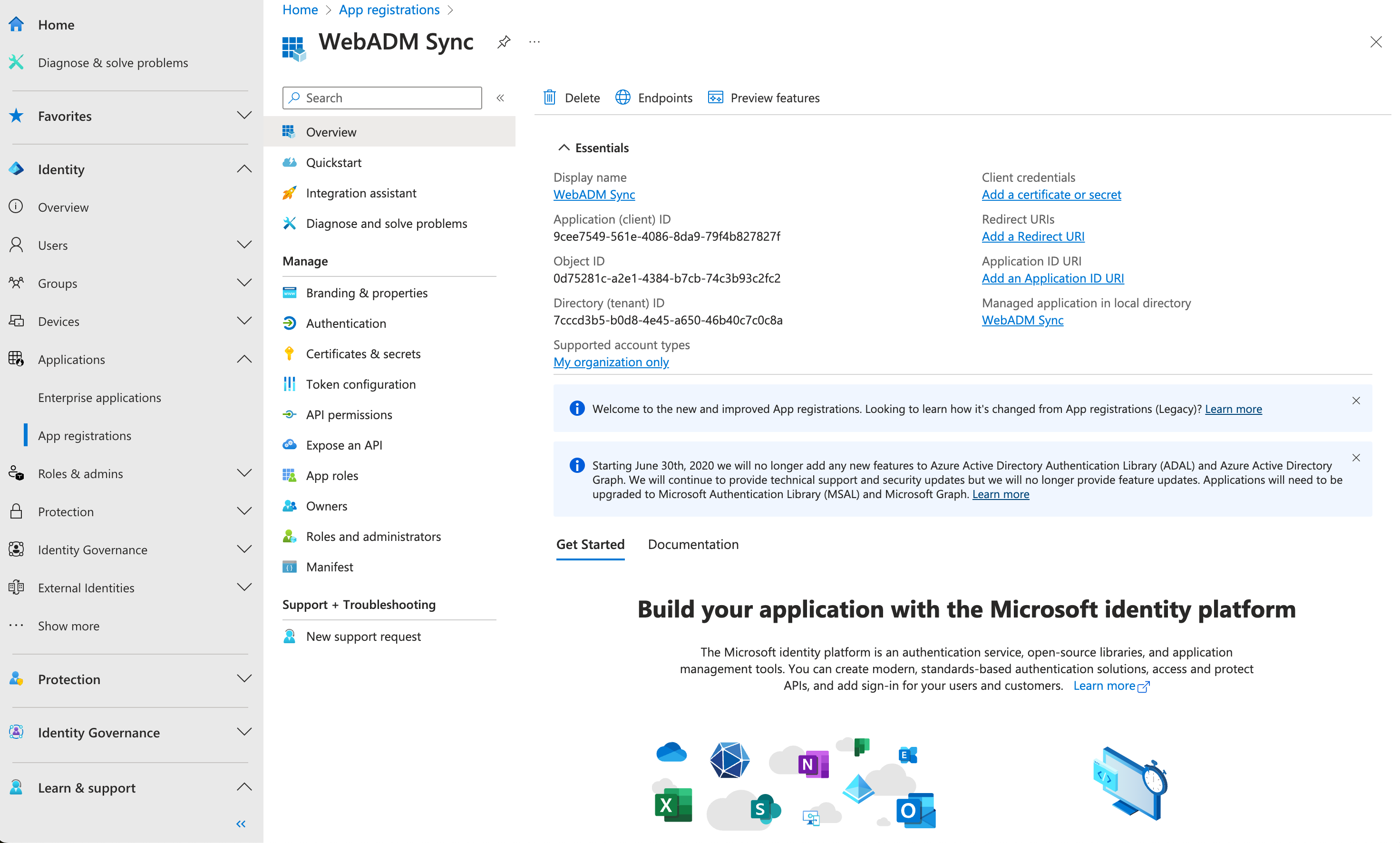
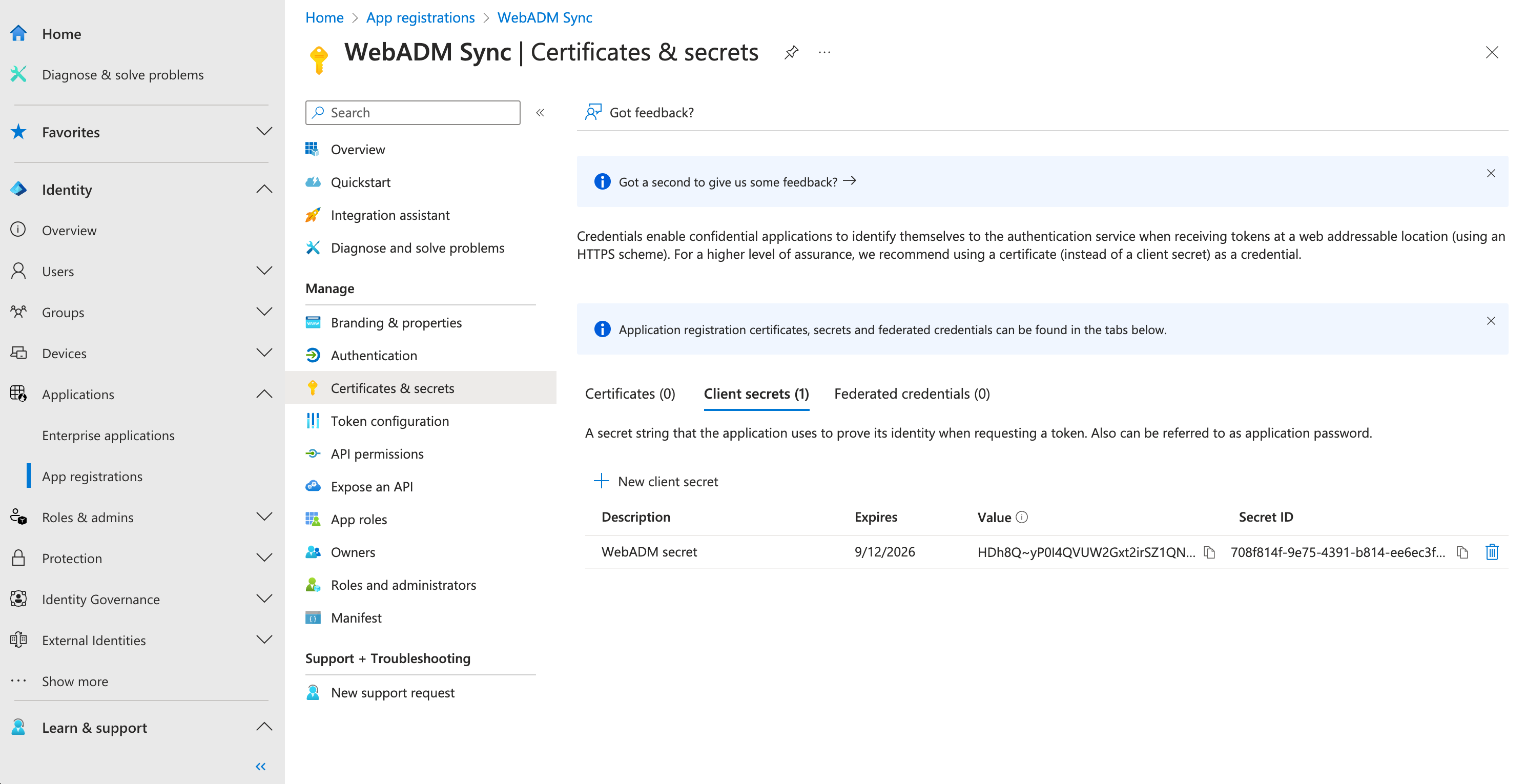
Now, navigate to the Certificates & secrets menu to create a new client secret. This is the last piece of information required by the WebADM Framework.
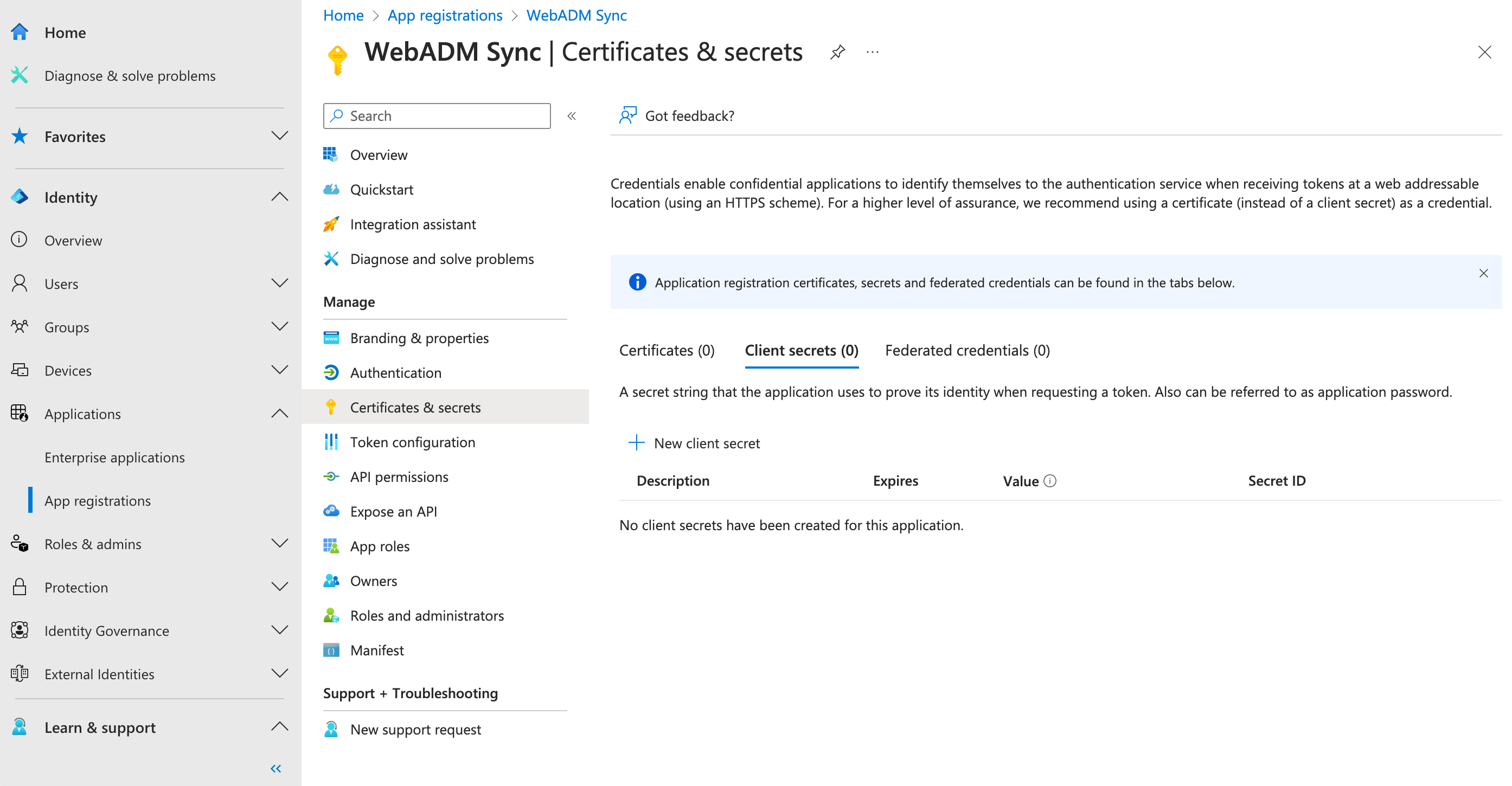
Click on + New client secret and define an expiration date. Note that when the client secret expires, it will need to be renewed and reconfigured in WebADM to maintain proper communication. Click on the Add button to complete the client secret creation.
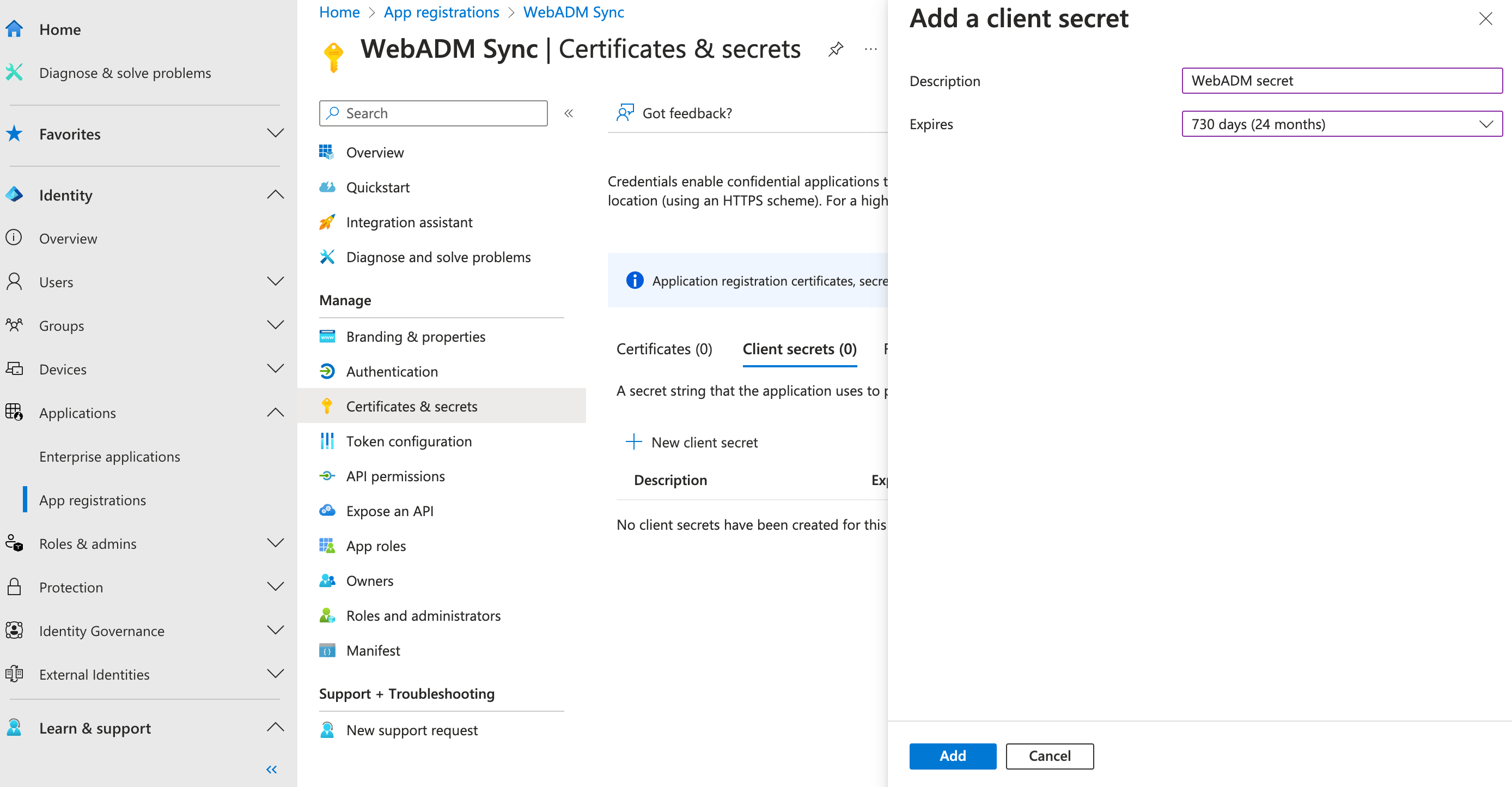
Once created, copy the client secret value to configure it in the WebADM Framework.
Permissions & Roles
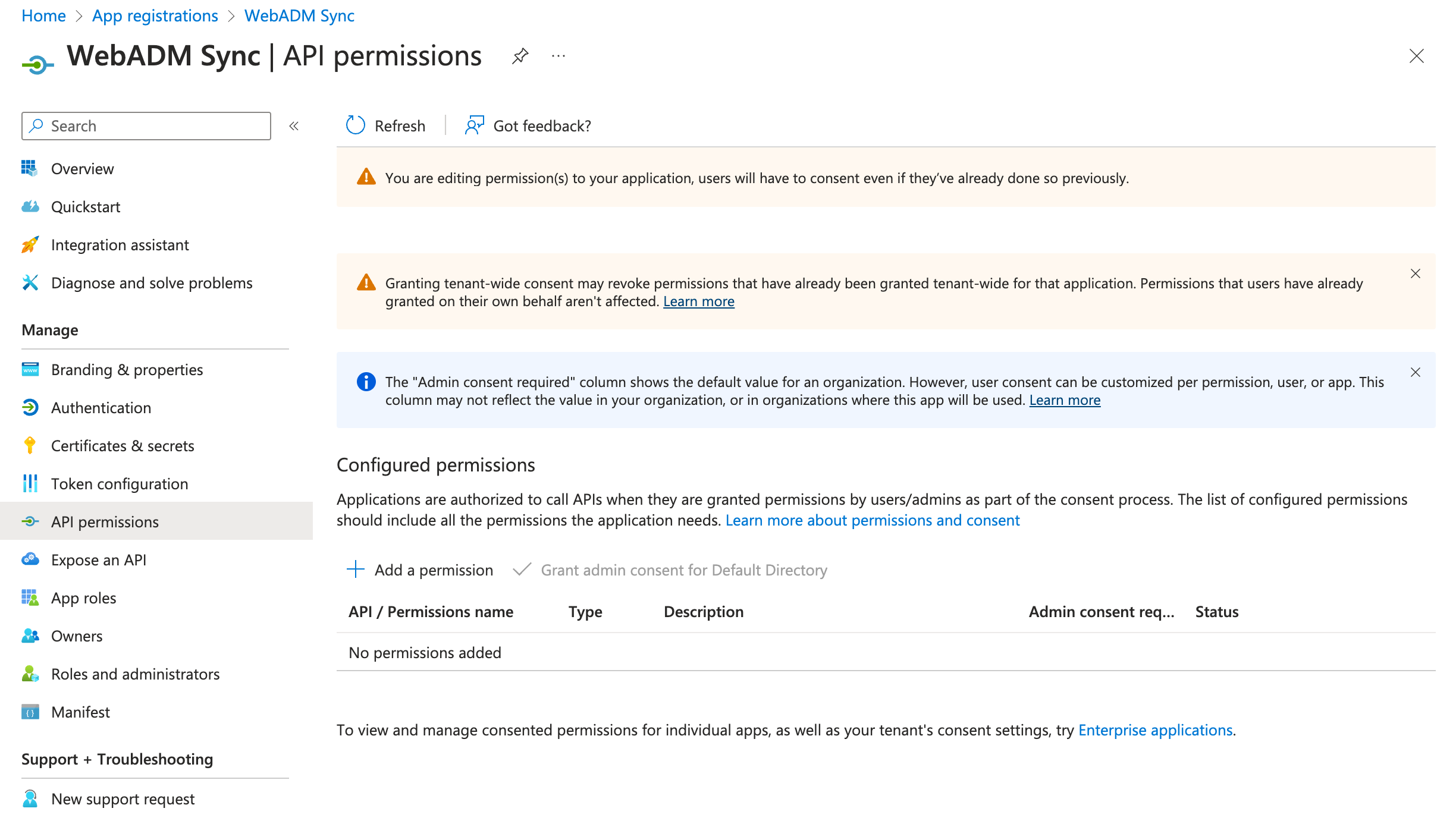
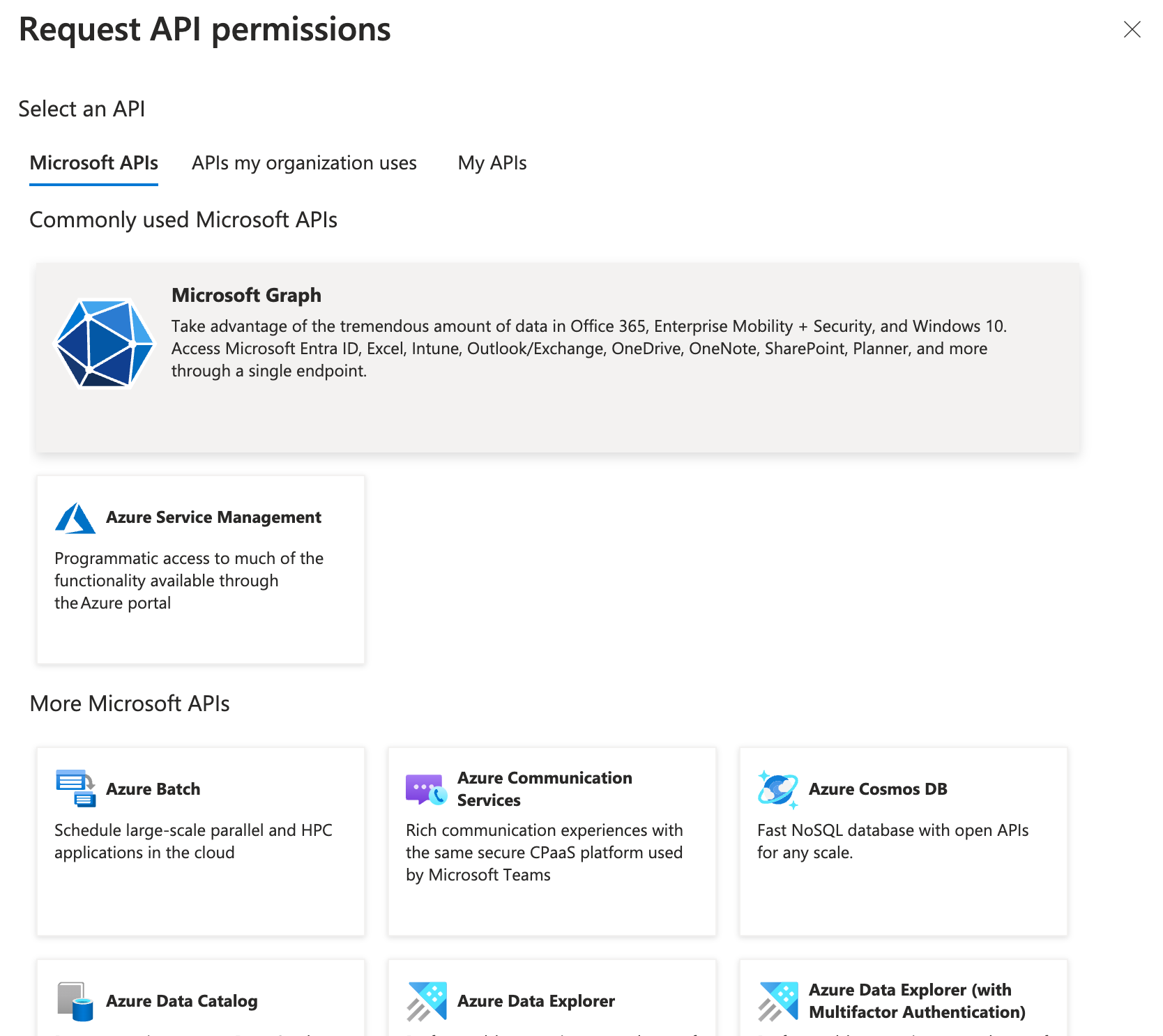
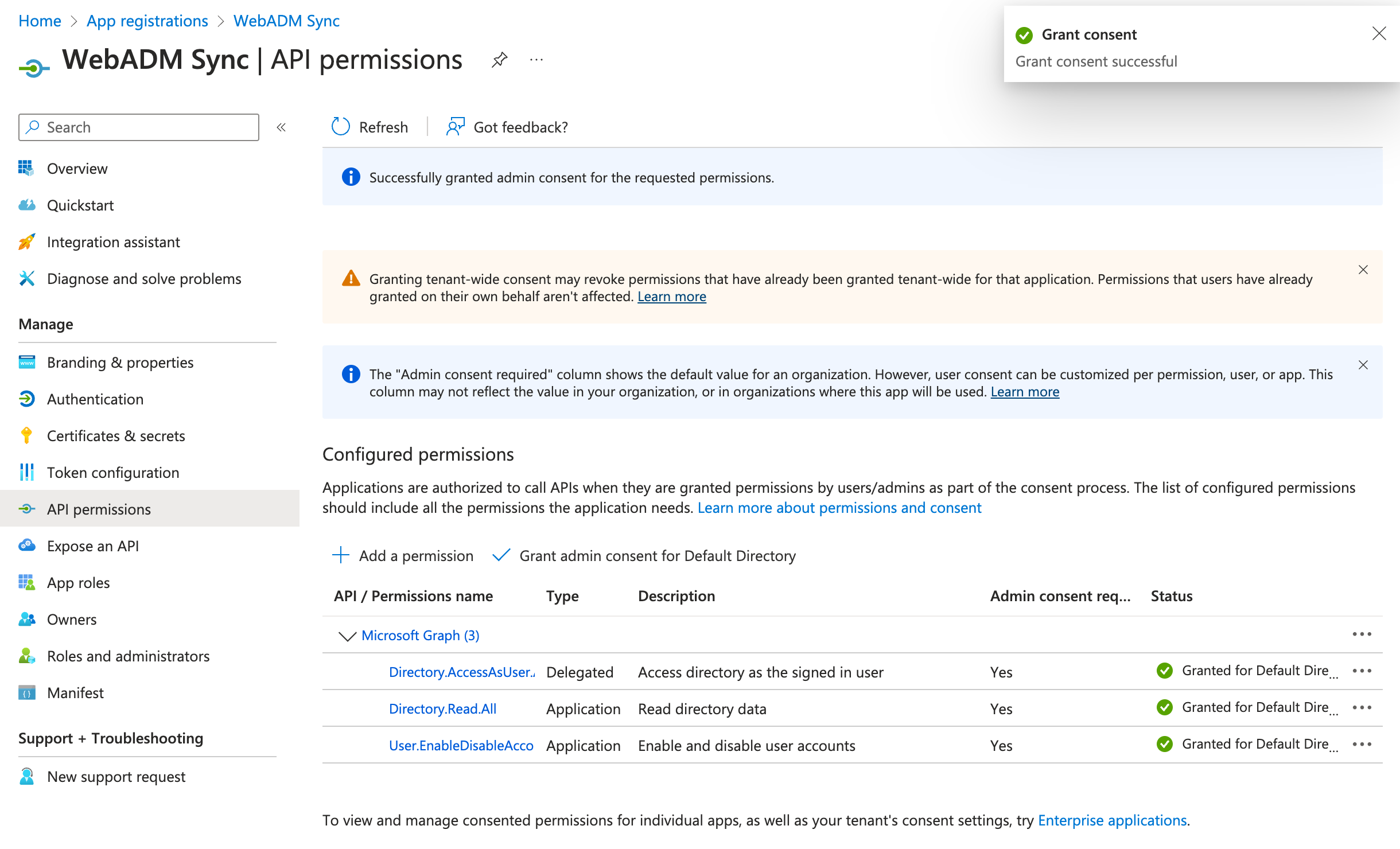
The following section provides information on the permissions that need to be granted to your application for the different features available in the WebADM framework. Navigate to API Permissions under your registered application.
Synchronize Users and Groups Information
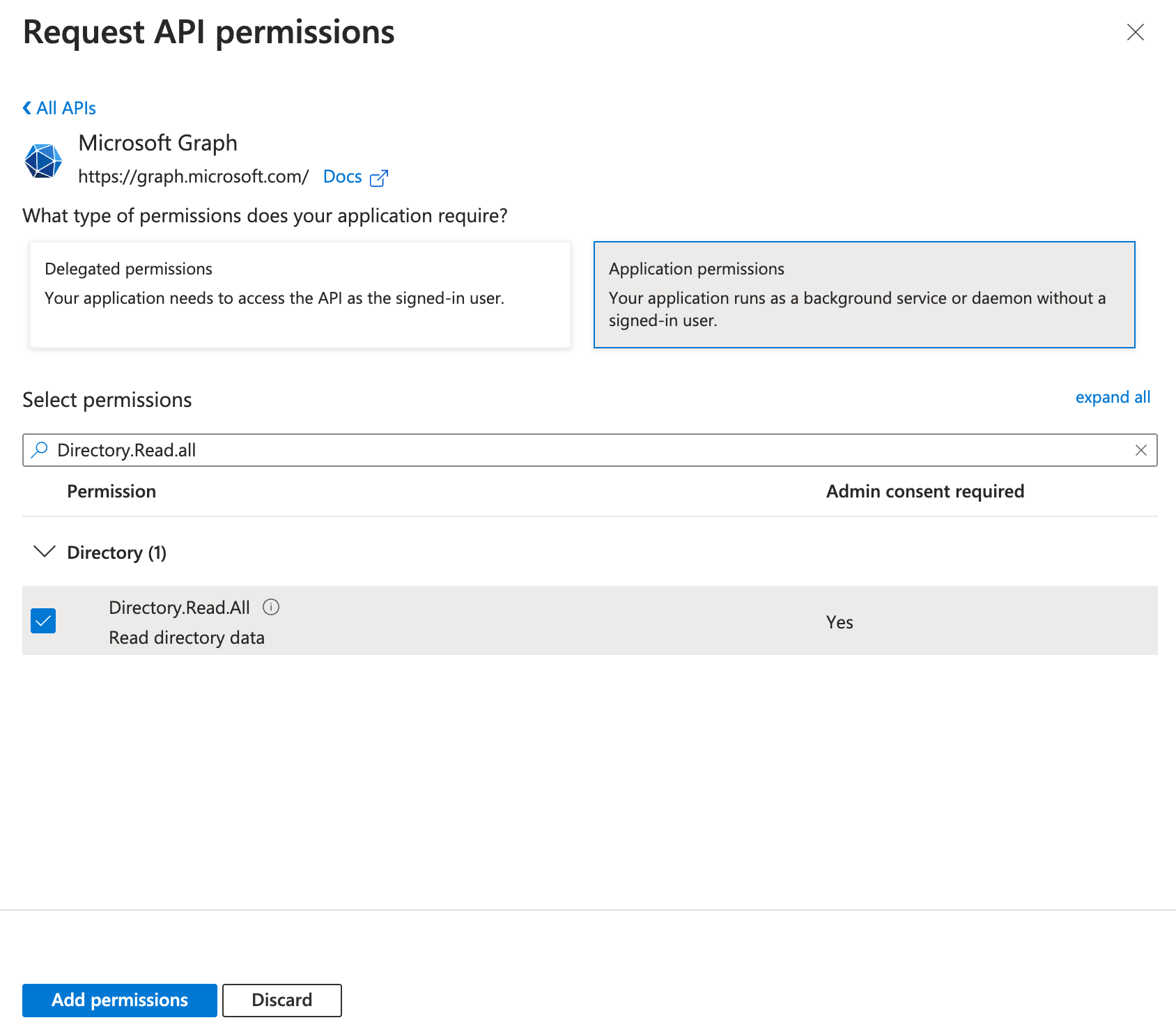
Usecase: Synchronize users and groups from EntraID within the WebADM Framework.
- Type: Application Permission
- Permission Required:
Directory.Read.All: Read directory data. - Description: Allows the app to read data in your organization's directory, such as users, groups and apps, without a signed-in user.
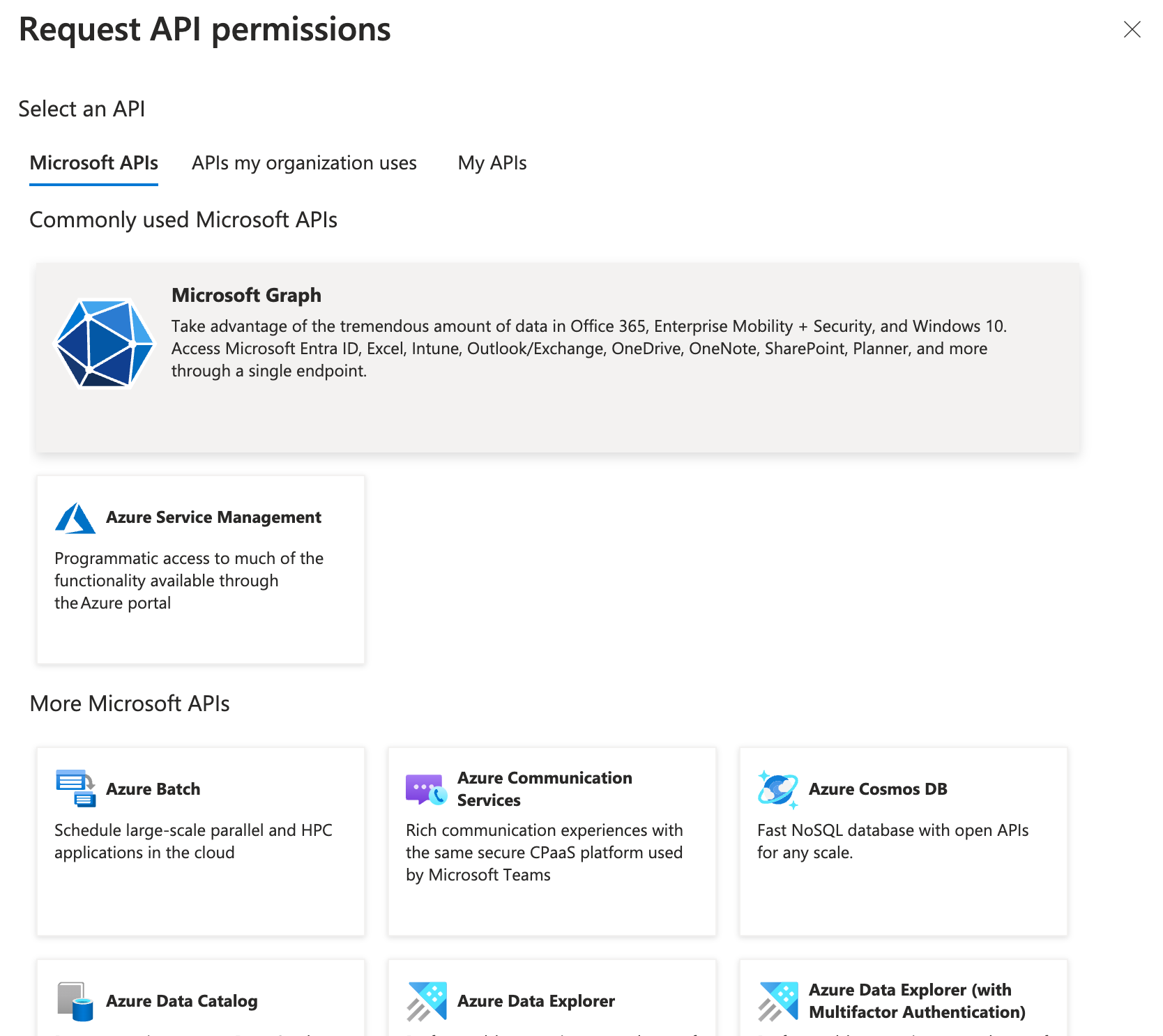
Click on + Add a permission and select Microsoft Graph option, then Application permissions.
In the search bar, type Directory.Read.All and check the box next to the listed permission. Then click Add Permissions.
Password verification with EntraID
Use Case: Validate a user's password using Entra ID for authentication that started with OpenOTP and a synced Entra ID account.
- Type: Delegated Permission
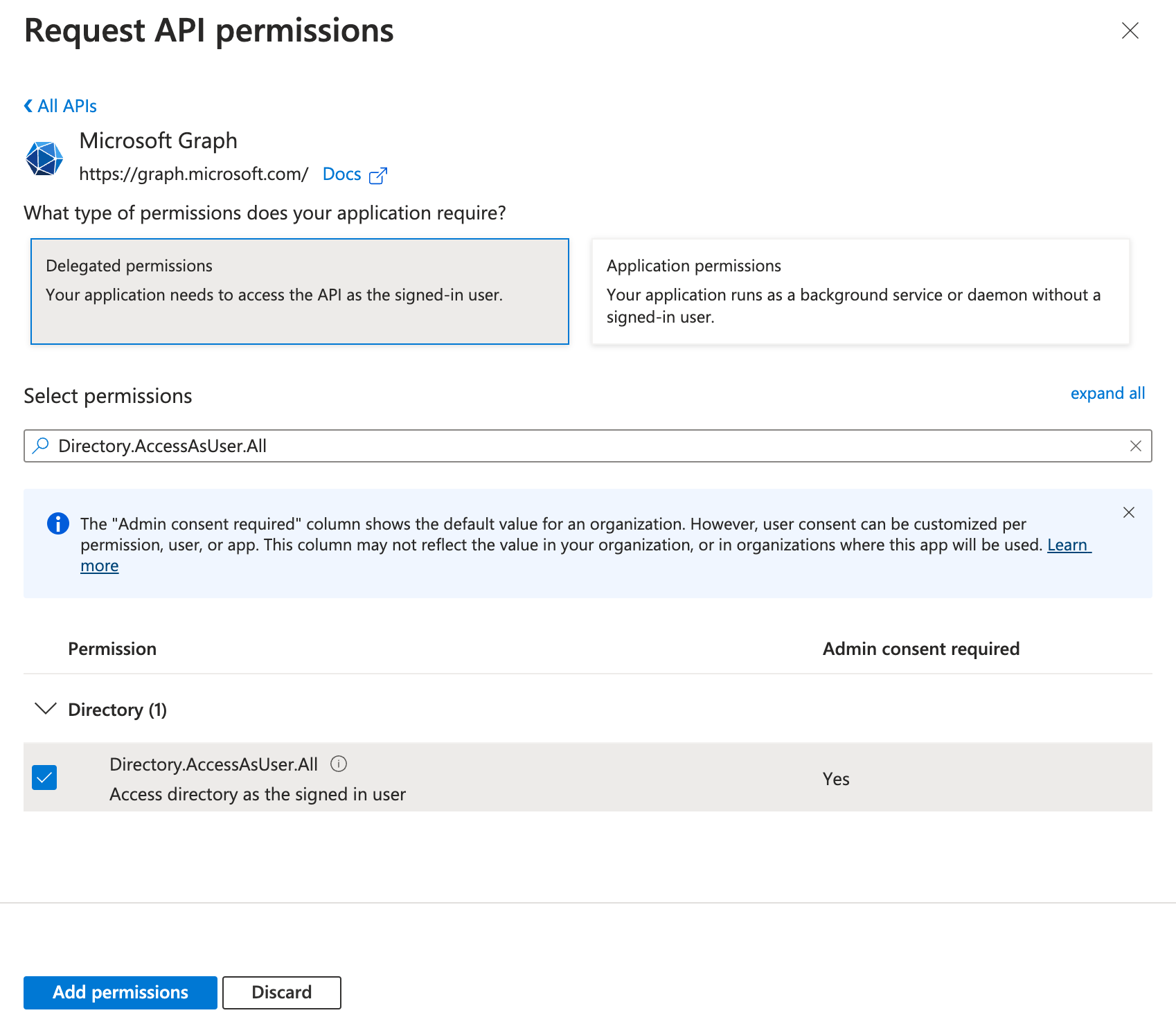
- Permission Required:
Directory.AccessAsUser.All - Description: Allows the app to have the same access to information in the directory as the signed-in user.
Click on + Add a permission and select Microsoft Graph option, then Delegated permissions.
In the search bar, type Directory.AccessAsUser.All and check the box next to the listed permission. Then click Add Permissions.
User Account Lockout
Use Case: This permission is essential when using the Account Lockout feature in OpenOTP Badging. It is required if you've implemented an account lockout policy that prevents access when the user is not badged-in. The account will remain locked at the Entra ID level, until the user badges-in with the OpenOTP Token application or from the User Self-Service Desk web application.
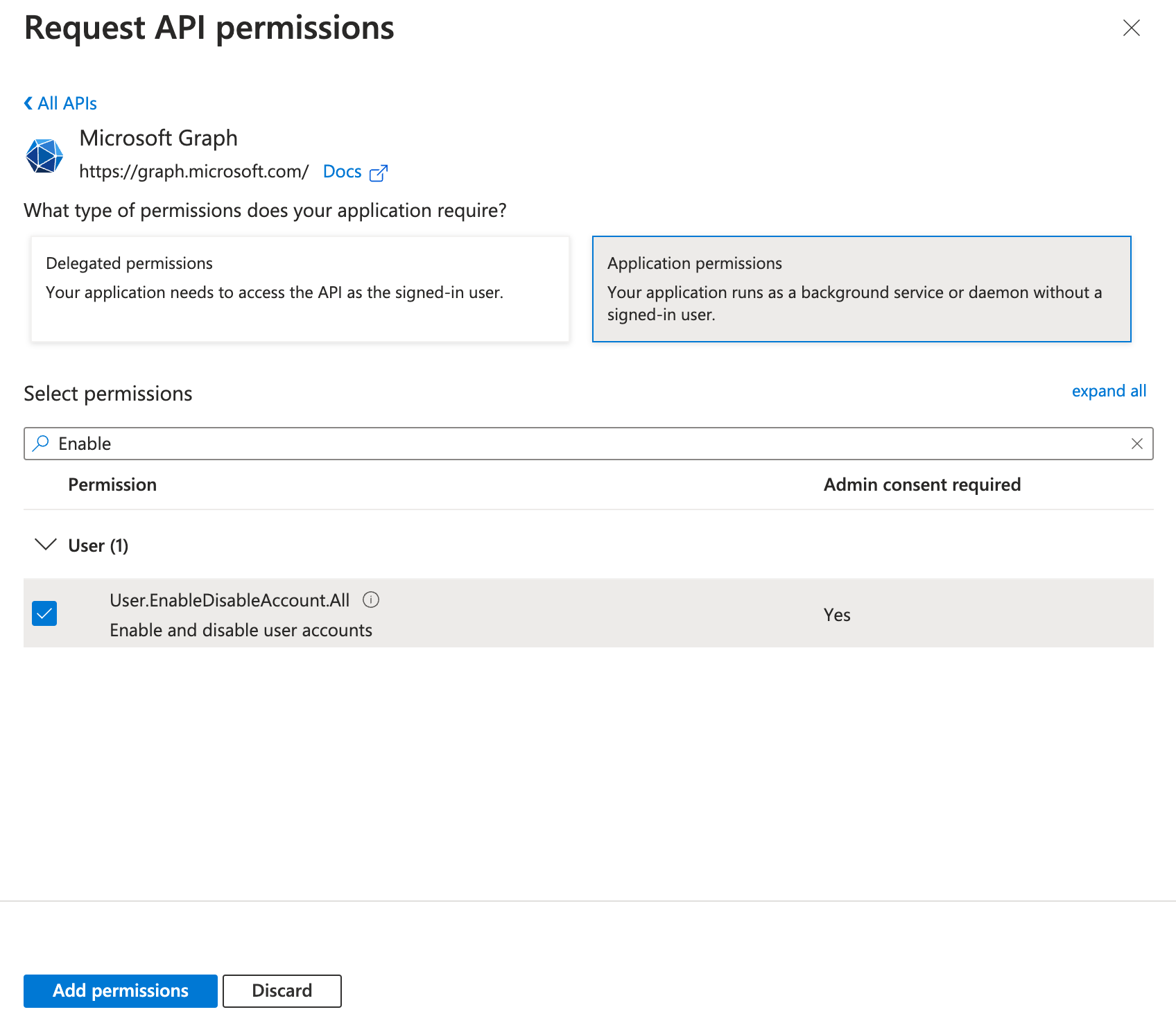
- Type: Application Permission
- Permission Required:
User.EnableDisableAccount.All - Description: This permission allows the application to read and write user profiles without a signed-in user. It is needed to perform operations such as locking a user account by updating the user's properties, like setting the account to disabled.
Click on + Add a permission and select Microsoft Graph option, then Application permissions.
In the search bar, type Enable and check the box next to the listed permission. Then click Add Permissions.
Password Reset/Update
Use Case: Passwords for EntraID accounts synced in WebADM can be changed through the WebADM Framework. The system supports applying password policies, leak protections, and weak password detection to EntraID accounts. Resetting a user's password from a third-party application requires admin rights due to the sensitivity and potential impact of this operation. In EntraID, the permissions required to perform these actions generally involve administrative privileges.
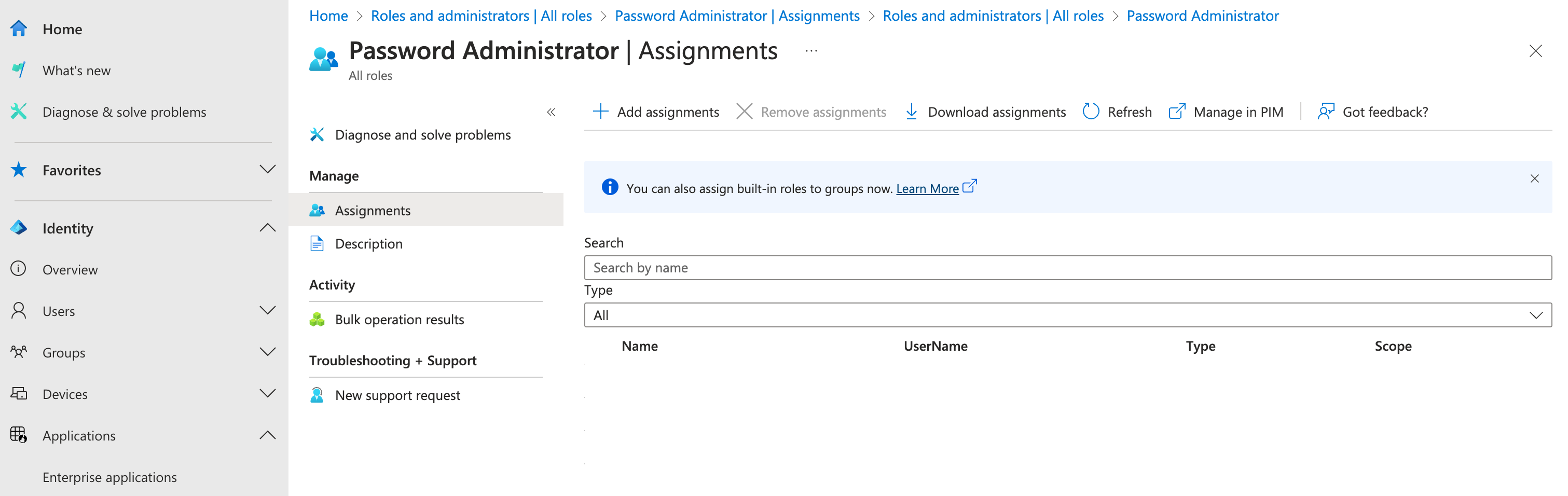
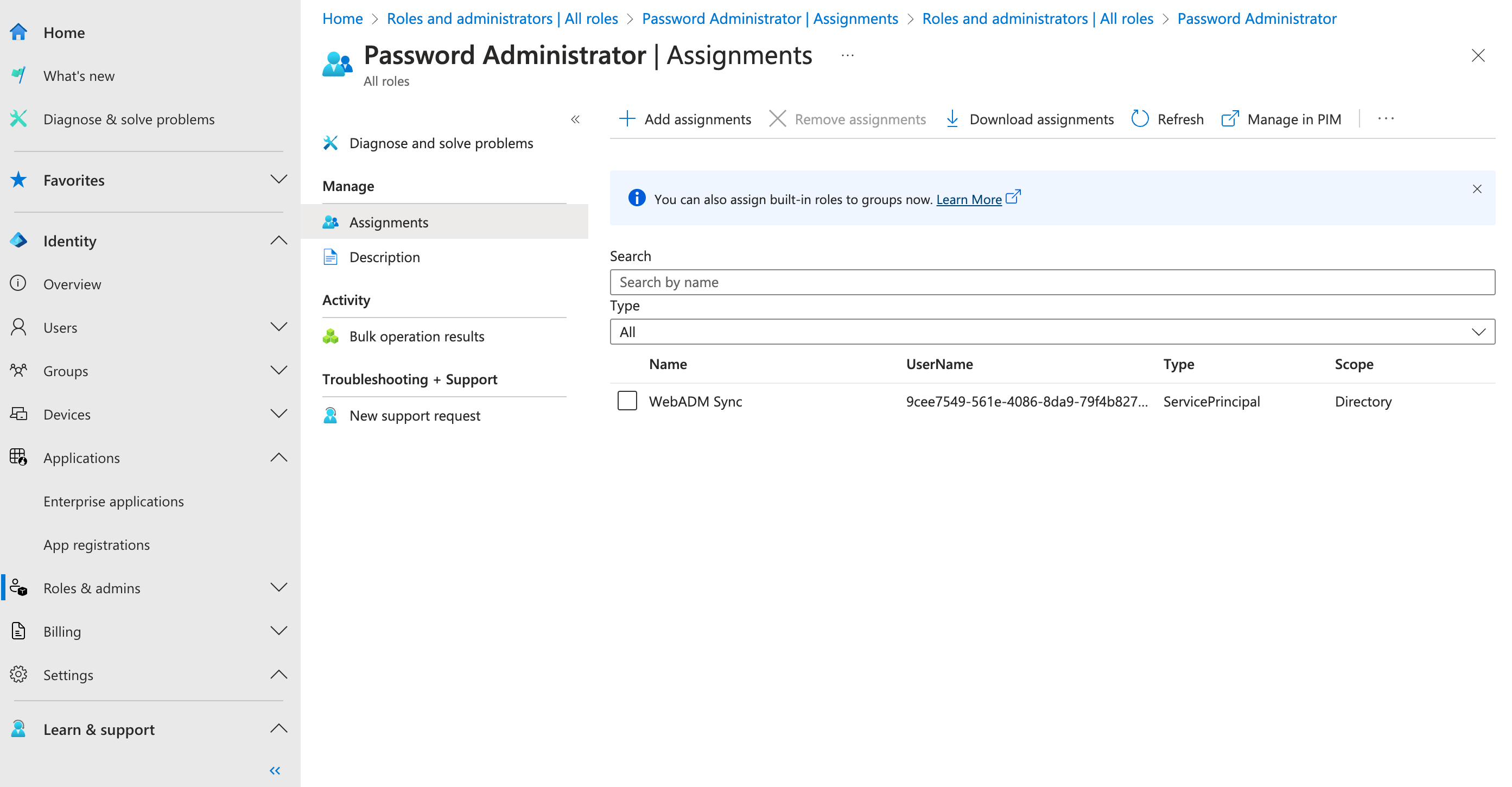
These permissions are not granted at the API Permissions level but rather at the Roles & Admins level. To assign the necessary permissions, go to the Roles & Admins section and search for the Password Administrator role in the search bar.
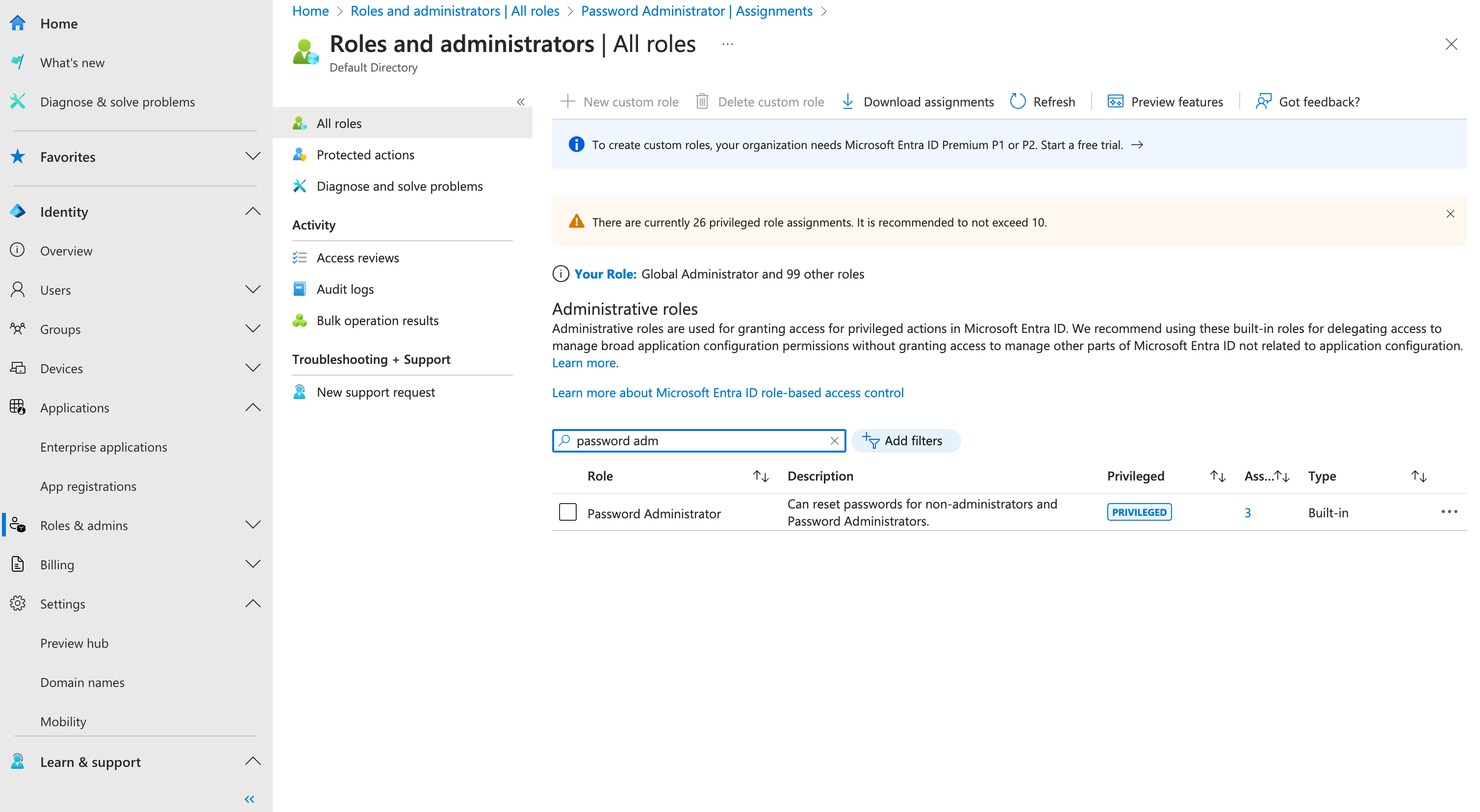
Click on Password Administrator role, then click on + Add assignments.
In the search bar, type the name of the previously created application (in this example, WebADM Sync). Check the box next to your application, then click the Add button.
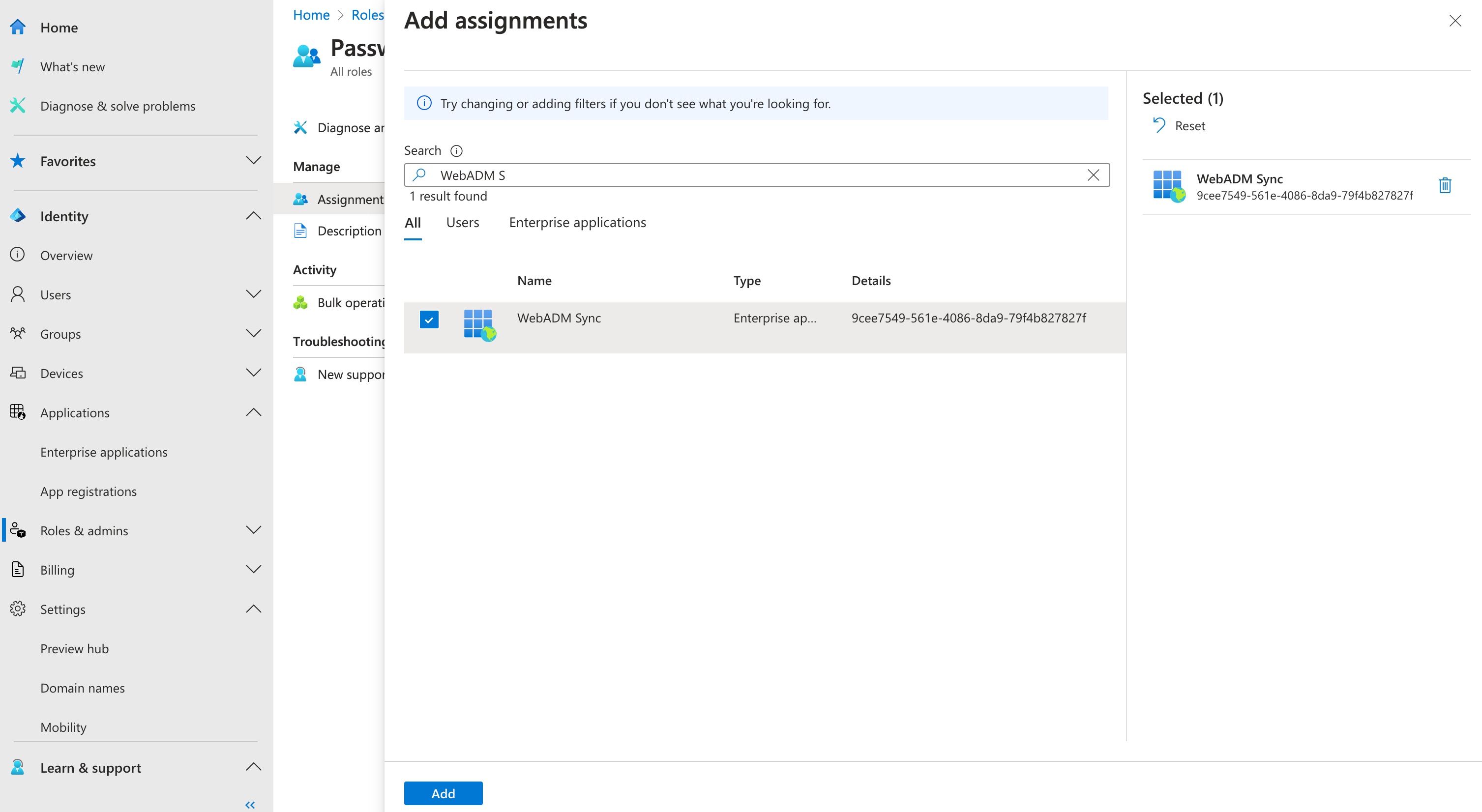
The Password Administrator role is now assigned.
Apply Permissions
Once your configured the needed permissions, from API permissions menu click on Grant Admin Consent.
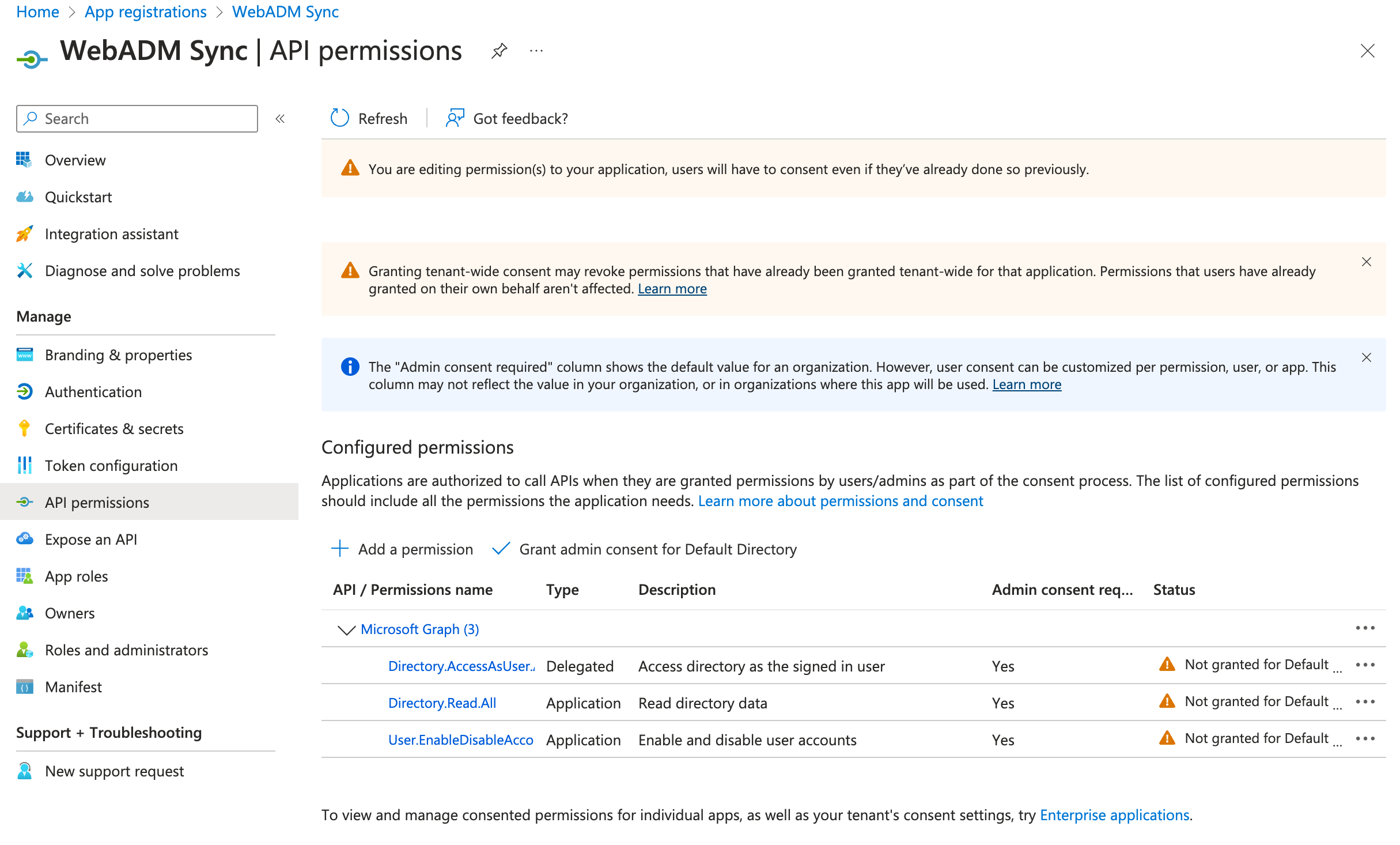
Click on Yes.
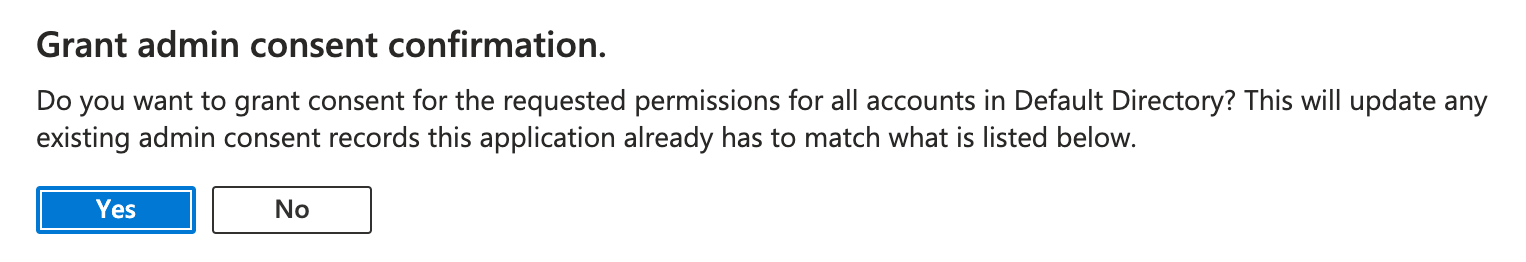
Permissions are now granted.
Entra ID Configuration for WebADM Password Verification
WebADM can remotely call Microsoft Entra ID APIs to verify user passwords, which is essential for applications integrated with WebADM/OpenOTP for MFA authentication. Since October 2024, Microsoft has enforced stricter MFA policies that may block remote password verification via API. To ensure proper integration, we recommend configuring a Conditional Access policy that bypasses MFA for the specific Enterprise or Registered Application previously created and used by WebADM.
Bypass MFA for WebADM Sync Registered Application
To configure a Conditional Access policy that allows the WebADM Sync Enterprise Application to validate user passwords without triggering Multi-Factor Authentication (MFA), follow these steps:
-
Sign in to the Microsoft Entra Admin Center
- Navigate to:
https://entra.microsoft.com - Ensure you have the necessary administrative privileges to create Conditional Access policies.
- Navigate to:
-
Access Conditional Access Policies
- In the left-hand navigation pane, select "Protection" > "Conditional Access".
-
Create a New Policy
- Click on "New policy" and name it:
Bypass MFA for WebADM Sync Enterprise Application.
- Click on "New policy" and name it:
-
Configure Assignments
-
Users or workload identities:
- Under "Include", select "All users" or specify the users/groups that will authenticate via WebADM.
-
Cloud apps or actions:
- Under "Include", click "Select apps" and choose the WebADM Sync Enterprise Application.
-
-
Set Access Controls
- Under "Grant", select "Grant access".
- Ensure that "Require multi-factor authentication" is not selected.
-
Enable the Policy
- Set "Enable policy" to "On".
- Click "Create" to finalize and activate the policy.
With this configuration, any authentication requests made through the WebADM Sync Enterprise Application will bypass MFA requirements, allowing seamless password validation for integrated applications.
EntraID configuration on WebADM
The EntraID configuration on WebADM consists of:
- Creating a Container, Organizational Unit, or Organization object in your LDAP tree where the EntraID tenant will be synced.
- Creating a WebADM
User Domainsand configuring the tenant information of your EntraID tenant.
Please note that the EntraID synchronization is performed in an OpenLDAP MountPoint, not in Active Directory.
Container Creation
Let's first create the container where objects will be synced in.
Login on the WebADM Administrator Portal with a super_admin account, and click on the Create tab.
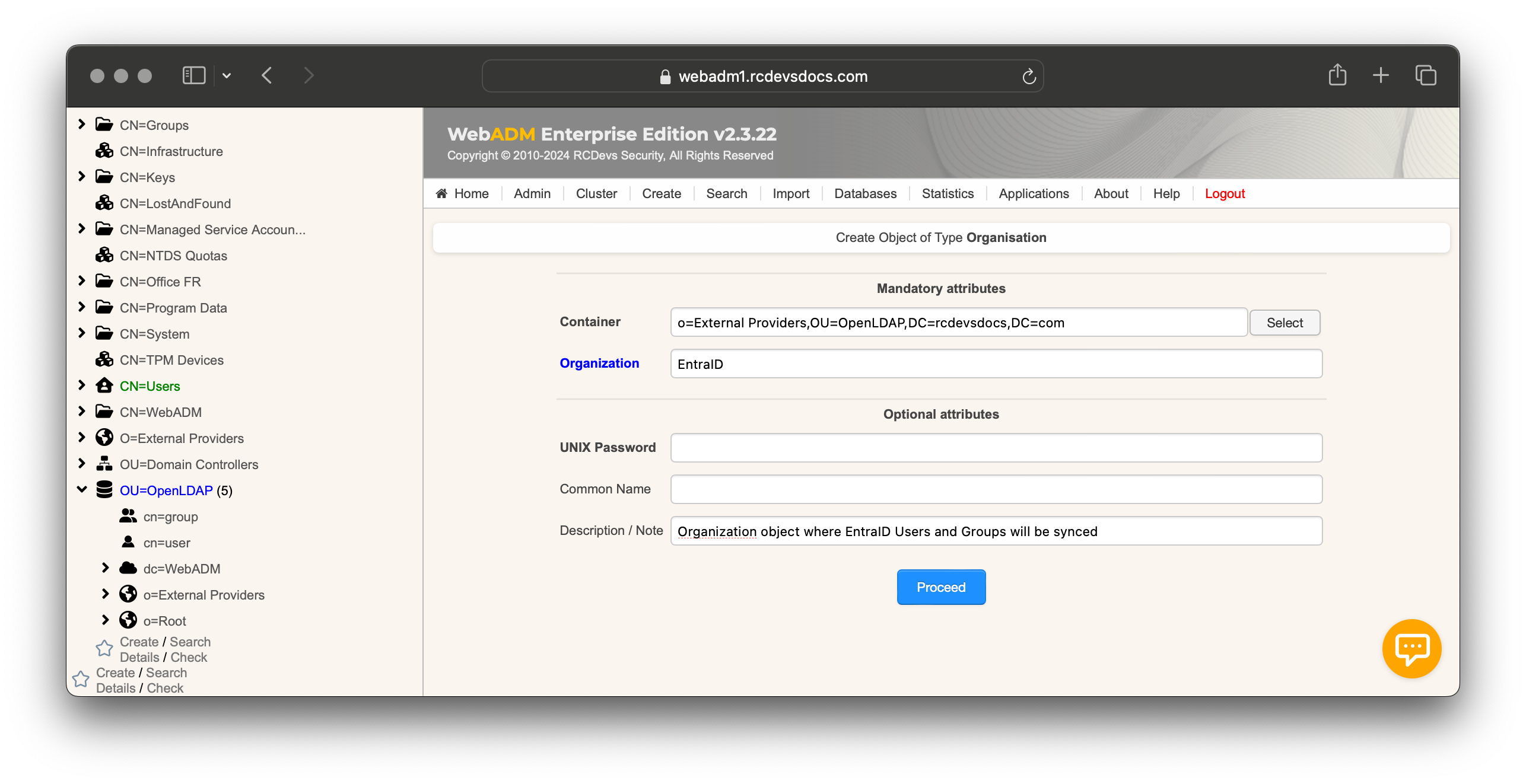
In this example, we create an Organization object named EntraID inside an existing Organization object named External Providers.
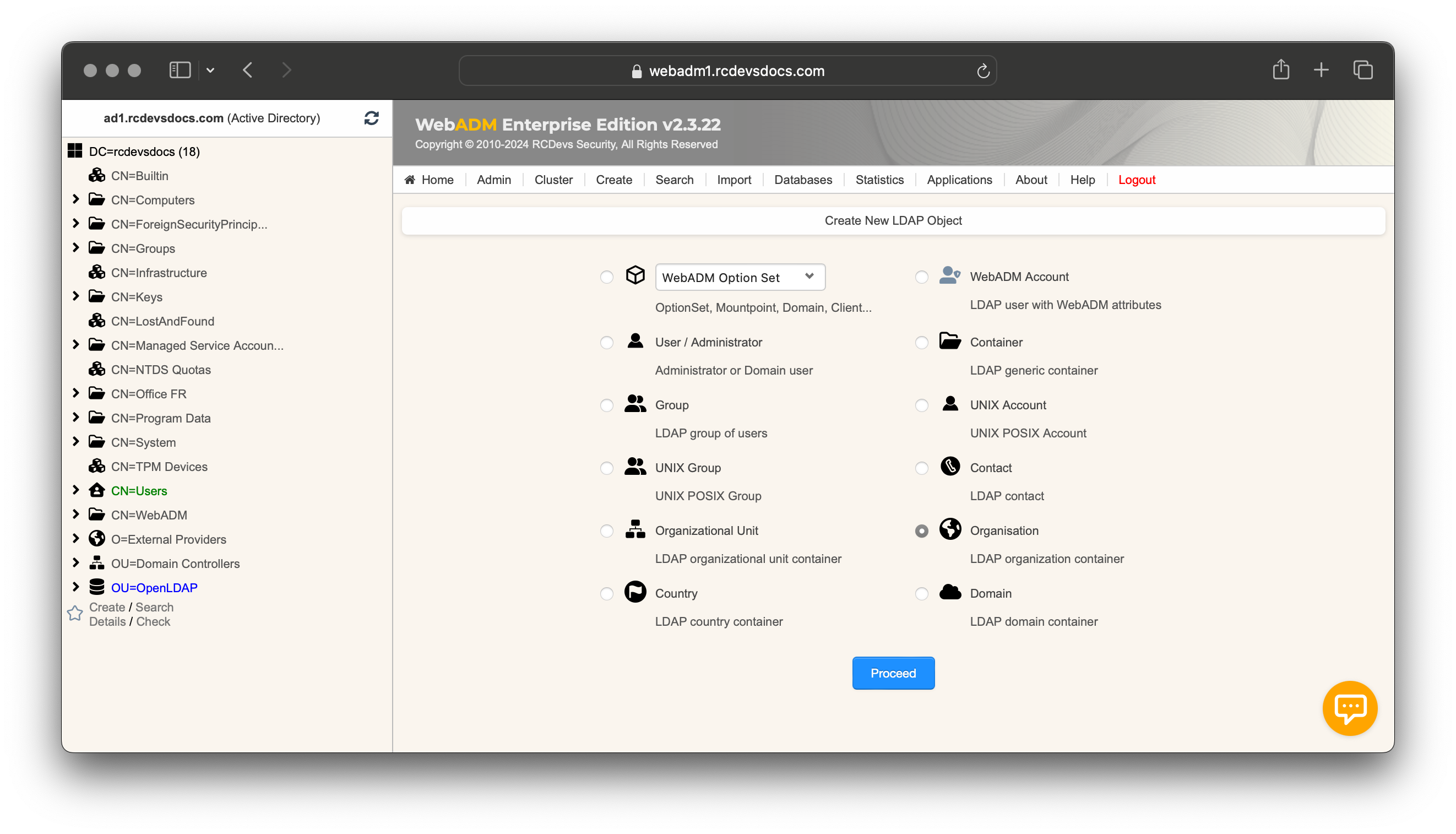
Click Proceed and select the location of the OU. I created it within an organization object named External Providers, but you can place it wherever you prefer. Name your object, optionally provide a description, and click Proceed, followed by Create Object.
Your organization object should then be created and visible at the location you specified.
Users and Groups structure
There are two possible ways to organize the users and groups that will be synchronized in WebADM:
-
Manual Container Creation: Once your organization is created, you can manually create two containers or OU the same way you created the Organization object—one to host synced users and another to host synced groups. In this scenario, you will need to configure the User Search Base and Group Search Base in the next section of this documentation, each pointing to their respective containers.
-
Automatic Container Creation Based on Entra ID Users' Department: If your Entra ID users have the
departmentattribute populated, the department value can be used to automatically build the LDAP structure. In this case, containers or OUs will be created dynamically based on the department values. Each department object that is automatically created will inherit the parent object type. In this scenario, you must enable theSubdiroption in theSync Optionsparameter in the next section. The User Search Base and Group Search Base can still be configured as described above, and department objects will be created under the Users container or OU. If the user's department changes, the move will be reflected in WebADM.
Domain Creation and Configurations
Username/UPN Concepts
The WebADM User Domain creation involves configuring the following key settings:
- The
User Search Base - The
UPN Modeand optionally theUPN Suffixwhen the UPN Mode is set toExplicit - The
Directory Synchronizationsettings
When configuring the UPN Mode, you are determining how the login name value will be synced in the login attribute.
Example for Clarification
Consider the UPN (User Principal Name) of an EntraID account: testaccount@xxxxx.onmicrosoft.com.
testaccountis the UPN prefix.xxxxx.onmicrosoft.comis the UPN suffix.
UPN Mode: Implicit vs Explicit
The UPN Mode can be set to either Implicit or Explicit. Here's how each mode works:
-
Implicit Mode:
In this mode, thetestaccountvalue (the UPN prefix) will be stored in the login attribute. With this mode, users can authenticate using two different methods:- By providing
username=testaccountanddomain=WebADM_Domain_Nameto the OpenOTP APIs. - By constructing a UPN with the
UPN Suffixconfigured in the WebADM domain object they belong to and logging in asusername@upn_suffix.
- By providing
This mode is the most flexible.
The UPN suffix can also be configured to work with the full UPN, even if it's not synced into the uid attribute.
With Active Directory backend configured with WebADM, you must set UPN Mode to Implicit. Explicit mode can not work, as the UPN prefix is synced into the sAMAccountName and the full EntraID UPN is synced into the UserPrincipalName.
- Explicit Mode:
In this mode, the full UPN (testaccount@xxxxx.onmicrosoft.com) will be stored as the login attribute. In this case, users must use the full UPN as their username to log in. Thetestaccountvalue (UPN prefix) alone cannot be used for authentication.
If the directory backend configured with WebADM is Active Directory, and you attempt to sync EntraID accounts into Active Directory, the prefix of the UPN will be synced into the sAMAccountName attribute, while the entire EntraID UPN will be synced into the UserPrincipalName attribute.
Now that you fully have the concepts, we can continue by creating the WebADM User Domain object and configuring the information for EntraID.
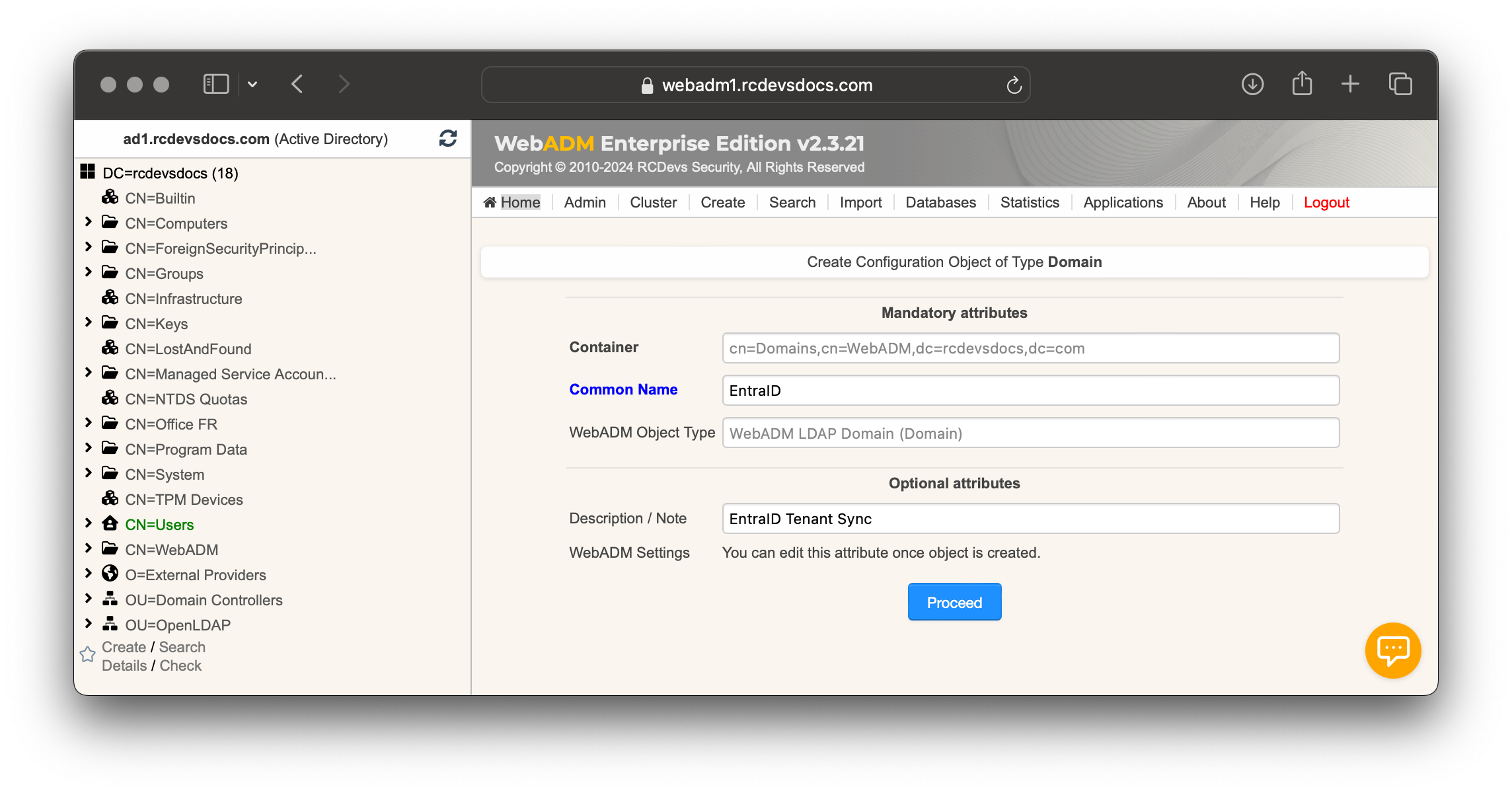
Go to the Admin tab, select User Domains, and click Add Domain. Provide a common name to identify the cloud provider, such as EntraID, and optionally add a description. Then, click Proceed followed by Create Object.
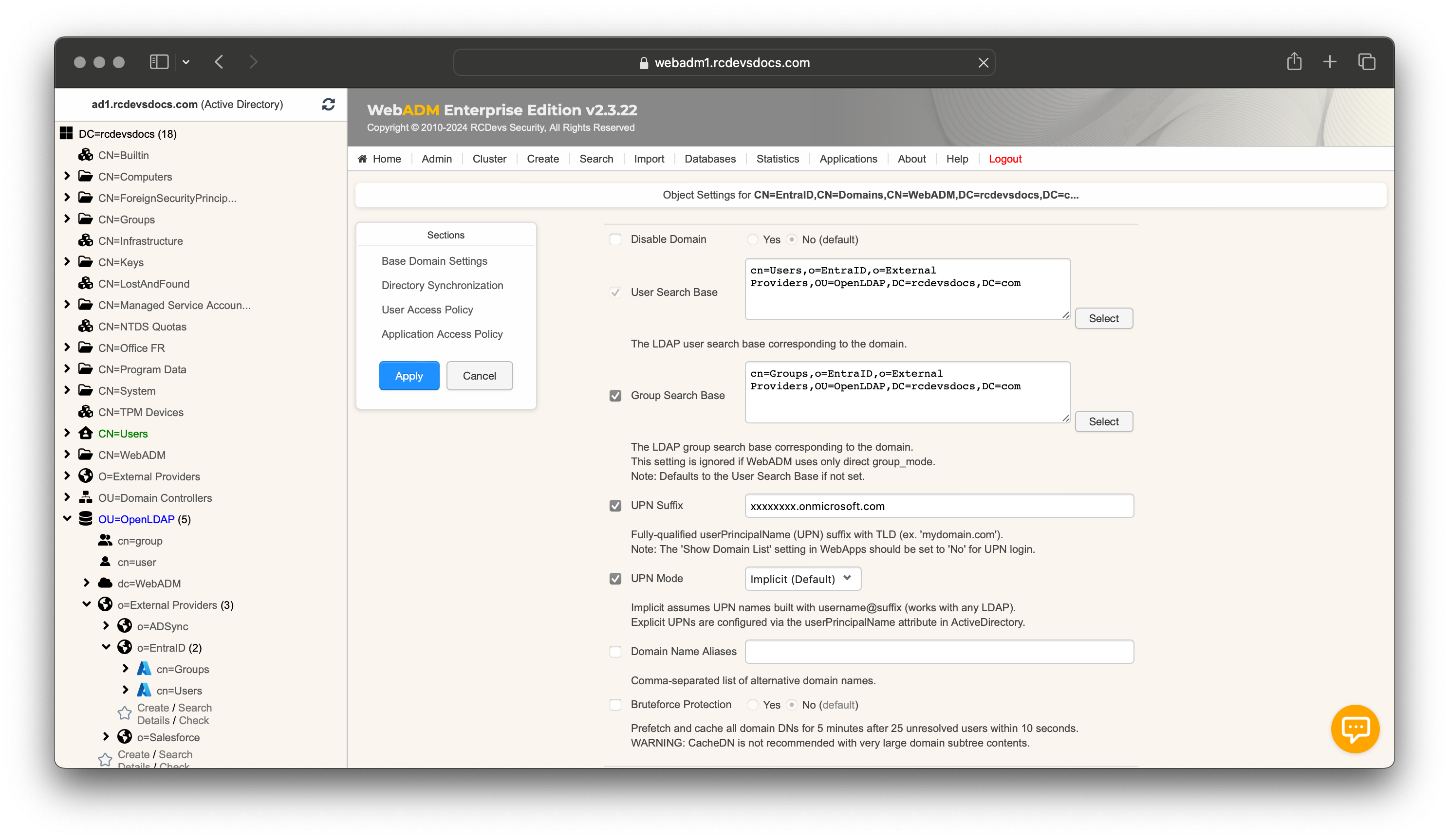
The domain object will be created, and you will enter the User Domain configurator. In the first section, configure the User and Group Search Bases to point to the Organizational Unit (OU) you previously created. In the UPN Suffix field, enter your EntraID UPN ending with onmicrosoft.com. This information can be retrieved from your tenant.
Scroll down to the Directory Synchronization section.
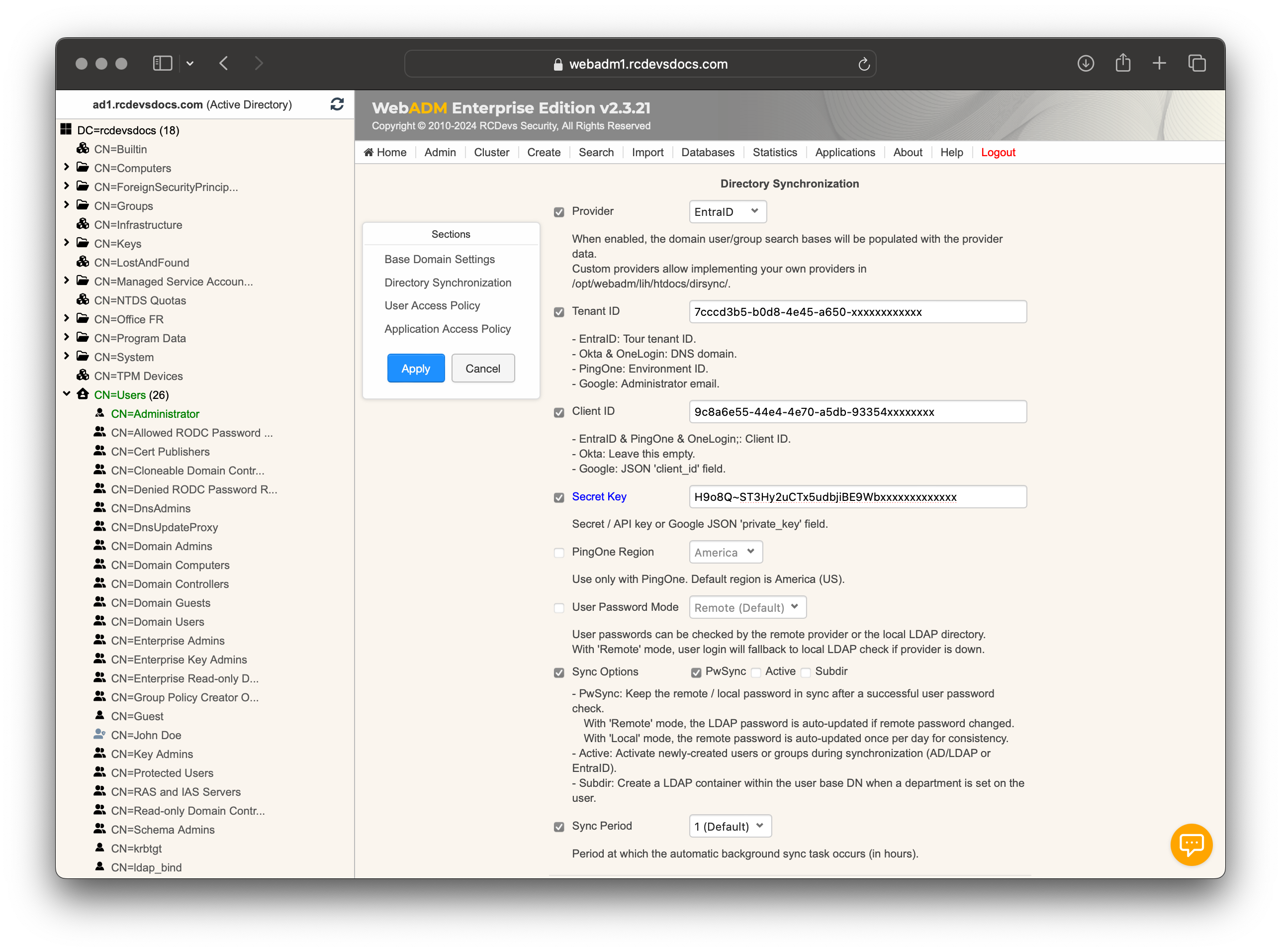
-
In the
Providersetting, selectEntra ID. -
In the
Tenant IDsetting, enter your tenant identifier, which can be retrieved from your Entra ID directory. -
In the
Client IDsetting, enter the unique identifier assigned to your registered application within the directory. -
In the
Secret Keysetting, enter the private key associated with the application. This key, used together with the client ID, verifies the application's identity. -
User Password Mode:- Remote – check against Entra ID.
- Local – check against WebADM LDAP.
When PwSync is enabled:
-
Remote mode + PwSync → After each successful login, WebADM updates its local LDAP password if it detects the user changed it in Entra ID.
-
Local mode + PwSync → WebADM uploads its local password to Entra ID once per day.
If PwSync is disabled, the password is merely validated with the LDAP.
- Choose the
Sync Optionsthat best suit your preferences synchronization, ensuring they align with the permissions granted to the application.
| Option | What it does | Fine points & caveats |
|---|---|---|
| PwSync | Keeps remote and local passwords identical after authentication, following the rules above. | • Works only after a successful password check. • Direction depends on current User Password Mode. • Daily push in Local mode occurs at the first login after 00:00 server time. |
| PwCopy | Lets you copy or move users between synced domains without forcing a password reset. | WebADM stores a secure, encrypted copy of the password in its sync-cache just long enough to recreate it in the destination IAM. |
| TwoWay | Pushes attribute changes, group membership edits, and object creations/deletions made in WebADM to the remote IAM. | Enables full “manage from WebADM” workflow. Make sure the app permissions in Entra ID cover every object type you plan to write. |
| Active | Activates newly imported users or groups at the end of the sync run. | Activating a user consumes an OpenOTP licence; activating a group simply enables WebADM group-policy evaluation. |
| Subdir | Creates (and auto-maintains) sub-folders under the User Search Base based on the user’s department value. |
Perfect for large tenants: HR changes the department in Entra ID → user is relocated to the matching OU/Container within WebADM. |
Make sure to select the combination of sync options that aligns with your organization’s IAM policies, operational model, and data security requirements.
- Finish by setting the
Sync Period. By default, synchronization occurs every hour.
When the configuration is complete, click Apply to save your settings. You will be redirected to the Registered LDAP Domains menu, where your Entra ID domain should appear with a Sync Now button.
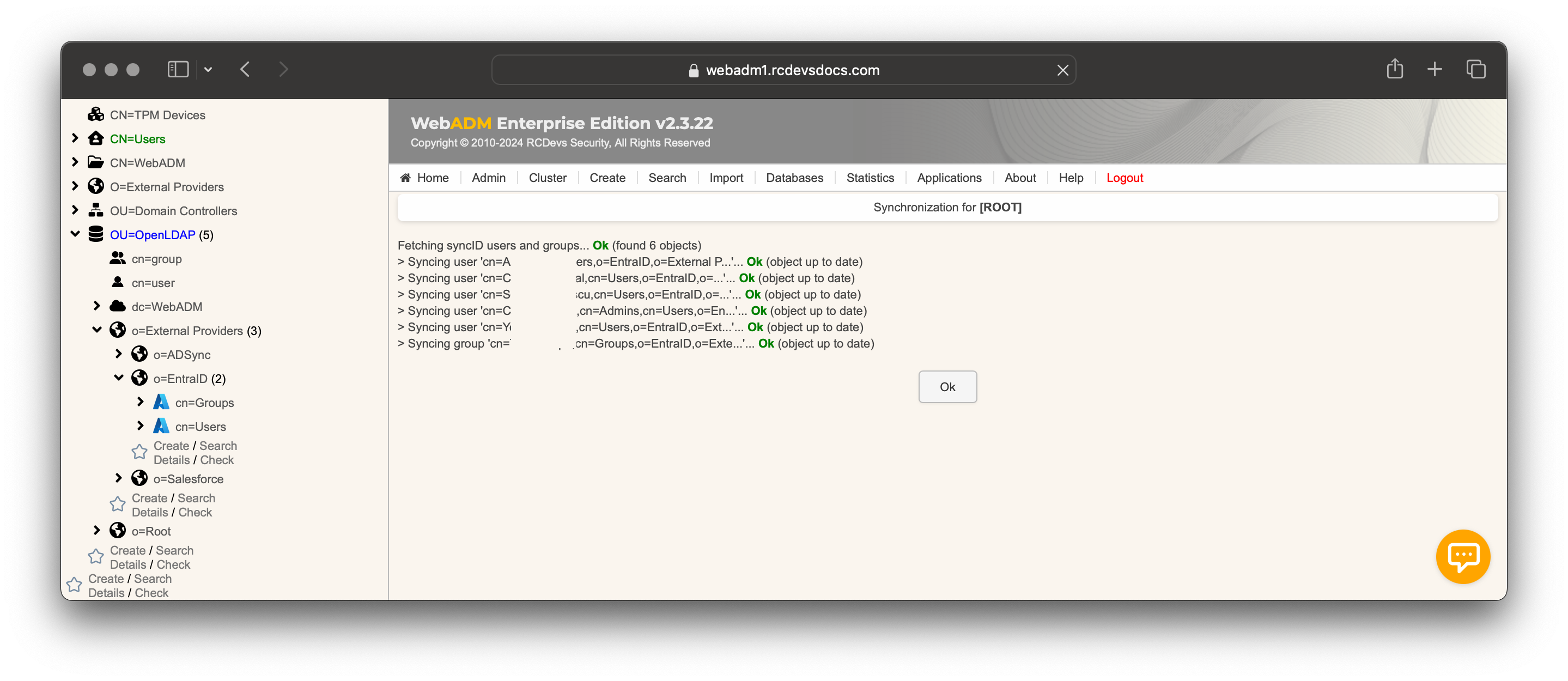
Click this button to start the synchronization process.
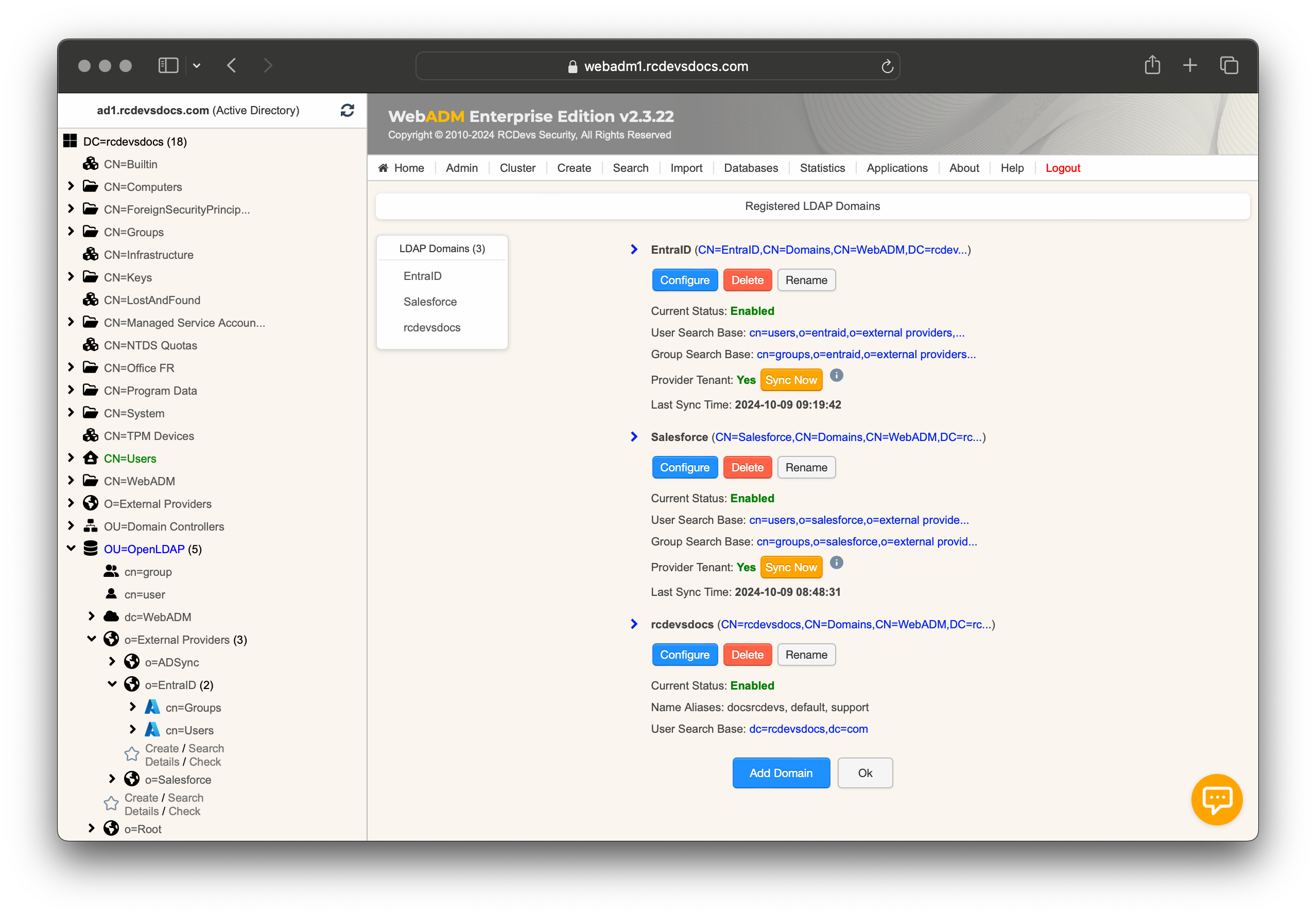
If any objects cannot be synced for any reason, an error message will appear in the synchronization output. For more details, consult the WebADM Server logs.
Objects that have been successfully synced will appear in the left LDAP tree, as shown in the screenshot below:
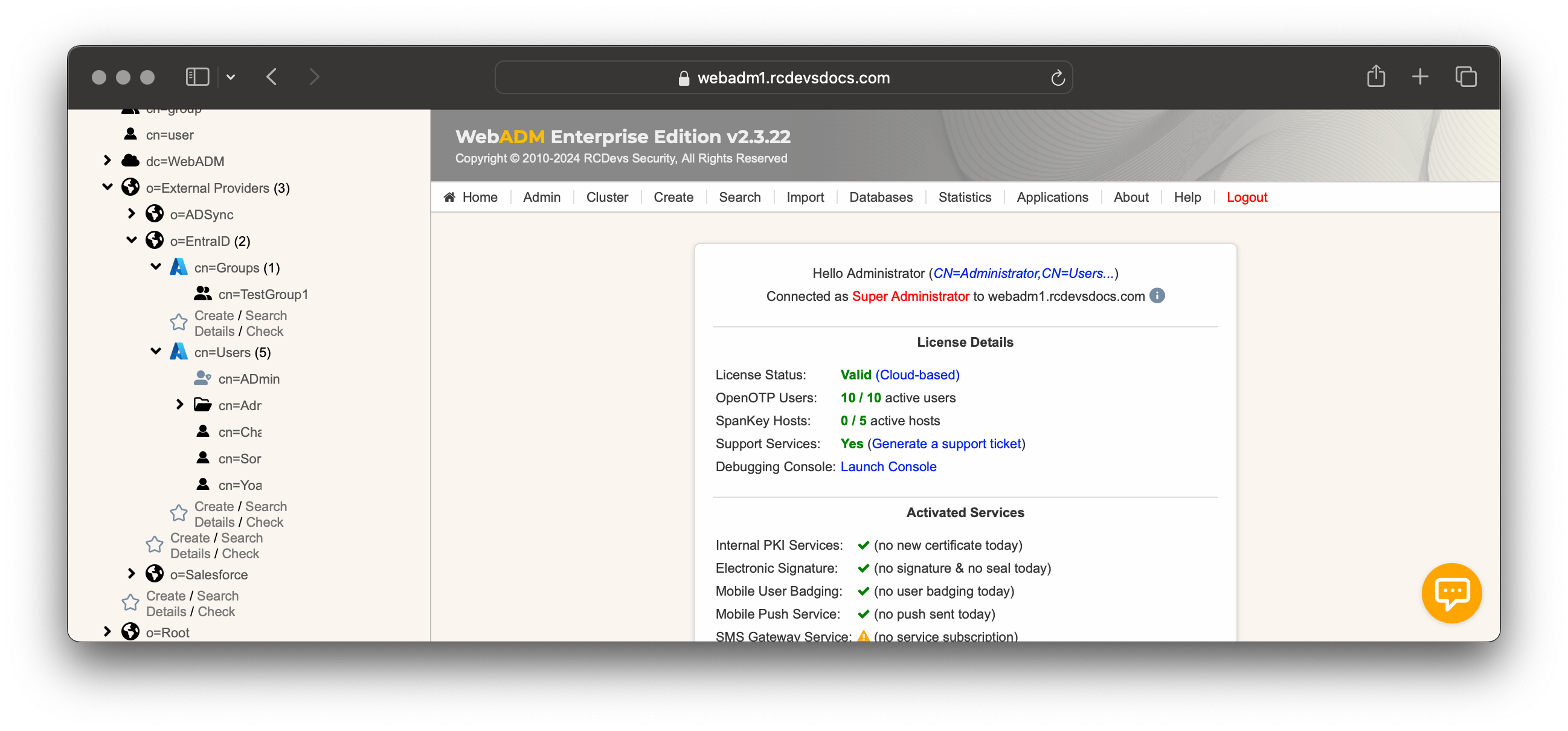
That's it. The synced identities and groups can now be used with WebADM, along with its dependencies and supported integrations.
Bidirectional User Synchronization and Attribute Mapping (Two-Way Sync)
As mentioned earlier, bidirectional synchronization has been supported since WebADM version 2.4.4. This feature allows you to edit LDAP attributes of synced objects directly from WebADM, and have those changes automatically reflected on the corresponding objects in remote IAM systems such as Entra ID.
This enables real-time, two-way identity updates, where both WebADM and external IAM platforms remain in sync without manual reconciliation. Any updates made to user attributes in WebADM will be synchronized back to the external provider in real-time. Please note that the requested change(s) may take some time to be reflected across Microsoft's distributed infrastructure.
Below is the attribute mapping used between WebADM LDAP attributes and Entra ID attributes for user objects:
| WebADM | Entra ID | Direction | Notes |
|---|---|---|---|
uid / sAMAccountName |
userPrincipalName |
← → | WebADM rewrites suffix on updates |
givenName |
givenName |
← → | |
sn |
surname |
← → | |
mail (update) |
mail |
← → | Read-only on create |
mail (create) |
mailNickname |
→ | Required when creating users/groups |
mobilePhone |
mobilePhone |
← → | |
preferredLanguage |
preferredLanguage |
← → | |
department |
department |
← → | Drives Subdir OU placement |
company (o) |
companyName |
← → | |
title |
jobTitle |
← → | |
street |
streetAddress |
← → | |
postalCode |
postalCode |
← → | |
city (l) |
city |
← → | |
state (st) |
state |
← → | |
| password | passwordProfile.password |
→ | Write-only; never pulled from cloud |
| lockout | accountEnabled |
← → | false = locked |
Only attributes listed in the sync configuration and supported by the external IAM provider will be synchronized. Ensure that write permissions are properly configured in both WebADM and the cloud IAM system to enable successful bidirectional updates.
Group Synchronization (One-Way and Two-Way)
By default, when using cloud providers, groups and their members are synchronized into WebADM. However, there are important considerations depending on whether you are using a One-Way or Two-Way synchronization setup. Note that nested groups are not supported — only direct group memberships will be reflected in WebADM.
One-Way Synchronization
In One-Way mode, groups and their memberships are retrieved from Entra ID and synchronized into WebADM.
- Group membership in WebADM is a direct reflection of Entra ID.
- It is not possible to add users to a synced group from within WebADM. Any such changes will be overwritten at the next synchronization.
- To manage custom groupings, you can create local groups in WebADM (i.e., groups not linked to Entra ID) and manually populate them with Entra ID users. These local groups and their members will remain persistent.
Two-Way Synchronization
In Two-Way mode, groups are still initially retrieved from Entra ID, but WebADM gains control over group management.
- You can create, delete, and manage group memberships directly from WebADM.
- Changes made in WebADM will be synchronized back to your Entra ID tenant.
- As with One-Way mode, you can create local groups that include Entra ID users. These groups will not exist in Entra ID.
- During the creation of a group in WebADM, after completing the required attributes, an intermediary screen will appear asking whether the group should be a local object:
- Select Yes to create the group only in WebADM.
- Select No to synchronize the group with Entra ID.
Additional Information
In WebADM, object color indicates its synchronization status:
- Red objects are local only (not synchronized with Entra ID).
- Green objects are synchronized with Entra ID.
In Two-Way synchronization mode, when creating a user from the WebADM interface, you can optionally set an auto-deletion date from the LDAP Actions section in the user view. The user account will be automatically deleted on the specified date from both the remote directory (Entra ID) and the local directory.

