WebADM Upgrade Guide to V2
1. Introduction
This document provides the necessary information for upgrading servers running WebADM v1.7.x to WebADM v2.0. WebADM v2 is a major release.
This document is not a guide for installing WebADM or its applications (Web Services and WebApps). Specific application guides are available through the RCDevs Online Documentation. WebADM usage manual is not covered by this guide and is documented in the RCDevs WebADM Administrator Guide. In this guide, we will consider a common installation scenario where WebADM is running in cluster mode with two active servers.
2. What is new in WebADM v2 ?
2.1 Major changes
2.1.1 Push and license services based on HTTP2
WebADM v2 comes with major changes that need to be considered before the upgrade for both enterprise and freeware customers.
-
Replaced Push Servers and License Servers with RCDevs Cloud microservices. RCDevs Cloud microservices provides access to RCDevs online services like OpenOTP Push notification in a much more efficient way. Your WebADM establishes a set of permanent HTTP2-TLS connections with RCDevs services which work via HTTP proxies, under which service requests are tunneled. This involves firewall rules adjustments for push and license services. In 1.x versions of WebADM, push and license services access were done through a custom protocol on following endpoints and ports :
-
push.rcdevs.com port 7000 TCP
-
license.rcdevs.com port 7001 TCP
Now the only outbound connection you need to allow is :
- cloud.rcdevs.com port HTTPS/443
Adjust your firewall rules before the upgrade to keep push and license services connectivities post-upgrade.
2.1.2 Freeware users need a license
A license is now mandatory even for freeware users. Freeware users can generate a license for free by themselves through the following URL.
Once you received your license by mail, you need to import it on your WebADM server in /opt/webadm/conf/ folder before starting WebADM. WebADM v2 without any license will prevent it to start.
The license is required in order to use RCDevs Cloud services. All your WebADM v1 freeware features are maintained.
2.1.3 VOICE Biometric Authentication
A new OTP type named VOICE is now available under OpenOTP configuration. This feature is under license for entreprise usage and included in freeware version.
Contact sales@rcdevs.com for VOICE licensing.
- You need OpenOTP >= 1.5.0 in order to use voice biometrics authentication.
- You need RCDevs Directory Server >= 1.0.10-3 which includes voice schema.
- For Active Directory with extended schema, a new attribute needs to be added into your schema. New attribute is named
webadmVoice. To add this new attribute in your schema, please refer to section 6 of this document. - For Active Directory not extended schema, the attribute used to store voice fingerprint is
audioavailable in user and inetorgperson objectclasses.
2.1.4 Support for PKCS#11 SCHSM USB device
- WebADM v2 currently supports Nitrokey and SmartContact HSM devices.
- YubiHSMv2 support will come later this year.
Documentations for configuring these purposes are available here : SmartCard HSM MirKey HSM
2.2 Minor changes
- Upgraded OpenSSL to version 1.1.1g (including security fixes).
- Upgraded embedded Redis server to version 6.0.3.
- Fixed issues with MountPoints having an empty LDAP base DN.
- Fixed license expiration issues with trial licenses.
3. Backup Your Server
Before upgrading, please back up your WebADM configurations on any WebADM server. Therefore, please follow this guide Backup & Restore, that covers backup and restore recommendations for a typical RCDevs solution deployment including WebADM, OpenOTP with Radius Bridge and RCDevs Directory Server.
4. Install the Upgrade Package
You will need to perform the following instructions on all the servers of your cluster.
4.1 Upgrade WebADM through RCDevs Repository
To upgrade RCDevs packages with the RCDevs repository, packages should be installed first through the repository. To install RCDevs repository and install packages through the repo, please follow the RCDevs Repository documentation.
To upgrade packages through the repository:
4.1.1 RHEL/CentOS
[root@localhost tmp]# yum update webadm
4.1.2 Debian/Ubuntu
[root@localhost tmp]# apt-get update
[root@localhost tmp]# apt-get install webadm
4.2 Upgrade WebADM through the Shell Script
-
Download the WebADM v2.x all-in-one package.
-
Copy the package on the servers with WinSCP or another SCP tool.
-
Connect the servers via SSH or Putty.
-
Uncompress the package with:
gunzip webadm_all_in_one-2.x.x64.sh.gz
Note
Please uncompress the GZ archive once copied on the Linux server and not under Windows!
- Run the upgrade tool with the commands:
[root@webadm1 tmp]# sh webadm_all_in_one-2.0.0-x64.sh
WebADM v2.0.0 (x64 bit) Self Installer
Copyright (c) 2010-2023 RCDevs Security SA All rights reserved.
A WebADM installation is already present in '/opt/webadm'.
Remove(R) or upgrade(U) or quit(Q)? U
Verifying package update... Ok
Are you sure you want to upgrade the WebADM installation in '/opt/webadm' (y/n)? y
Extracting files, please wait... Ok
Removing temporary files... Ok
Executing upgrade script for WebADM version 2.0.0
> Adjusting WebADM objects.xml file... Ok
> Adjusting WebADM webadm.conf file... Ok
> Adjusting WebADM servers.xml file... Ok
Resetting file permissions... Ok
WebADM has been successfully upgraded.
Restart WebADM (y/n) y
Checking libudev dependency... Ok
Checking system architecture... Ok
Checking server configurations... Ok
Found Trial license (RCDEVSSUPPORT)
Licensed by RCDevs Security SA to RCDevs Support
Licensed product(s): OpenOTP,SpanKey,TiQR
Starting WebADM PKI service... Ok
Starting WebADM Session service... Ok
Starting WebADM Watchd service... Ok
Starting WebADM HTTP service... Ok
Checking server connections...
Connected LDAP server: LDAP Server (192.168.3.60)
Connected SQL server: SQL Server (192.168.3.68)
Connected PKI server: PKI Server (192.168.3.64)
Connected Mail server: SMTP Server (78.141.172.203)
Connected Session server: Session Server (127.0.0.1)
Checking LDAP proxy user access... Ok
Checking SQL database access... Ok
Checking PKI service access... Ok
Checking Mail service access... Ok
Checking Cloud service access... Ok
Your WebADM server is now up-to-date.
4.3 Check post upgrade
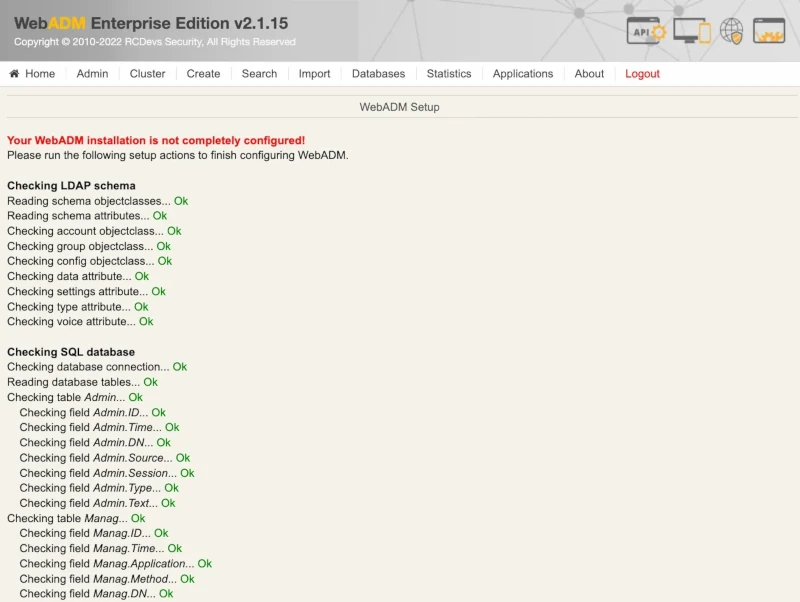
Once you upgraded WebADM and its dependencies, you have to log in on WebADM Administrator portal and check that the setup is completely done. You may have some new configurations who needs to be applied manually like new SQL table or column creation, new setting creation inside an application… Once logged on WebADM GUI, if there is any changes who need to be applied manually, you can see a warning message like below:
or like this if you already clicked on the Home tab:
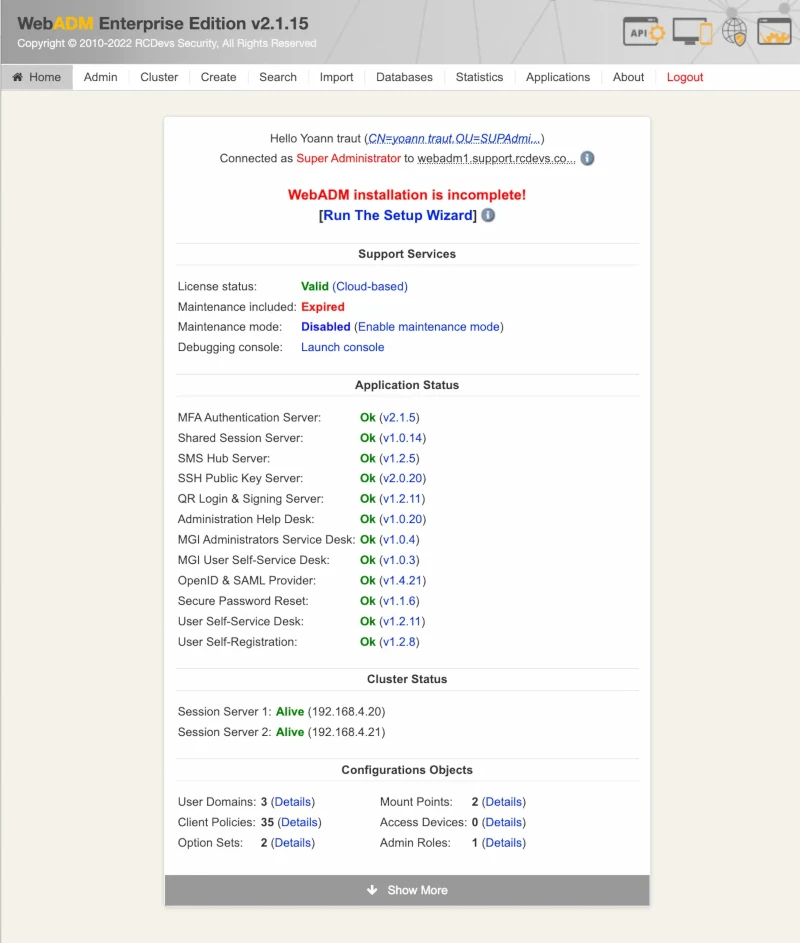
In that case click Run The Setup Wizard button to be redirected on the WebADM Setup screen and then click the blue button(s) (you may have multiple configurations to create) to finish the setup.

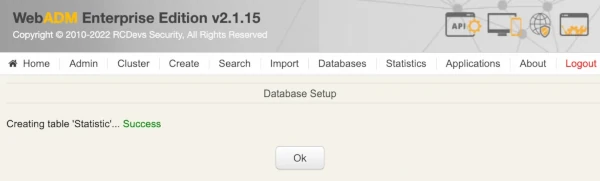
If you are running a WebADM cluster well configured, this extra operation should be done only from one WebADM node. Logout and login on the WebADM Admin Portal after finishing the graphical setup to double-check that everything is fine. Your update/upgrade is now finished and WebADM and its dependencies should be ready.
5. Check configuration files adjustements
The updater has automatically adjusted your configuration files. The most important configuration files are webadm.conf and servers.xml.
Find below, changes you can observe :
5.1 webadm.conf
5.1.1 Common to all setups
# Enable RCDevs cloud services such as OpenOTP mobile Push and license services.
# These features require a HTTPs outbound Internet access from the server.
cloud_services Yes
5.1.1 OpenLDAP, Novell, Active Directory schema extended
A new LDAP attribute which is commented out by default has been added :
#webadm_voice_attrs "webadmVoice"
If you want to use Voice biometric for authentication, you need to uncomment this setting and define the attribute in your Active Directory schema.
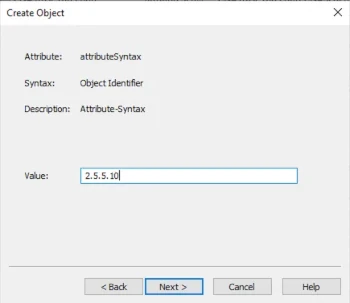
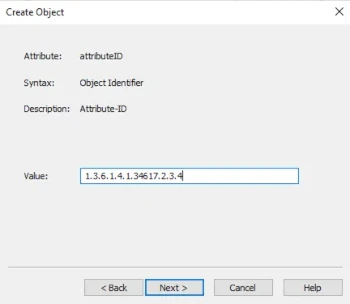
Below, the new attribute definition who must be part of your AD schema :
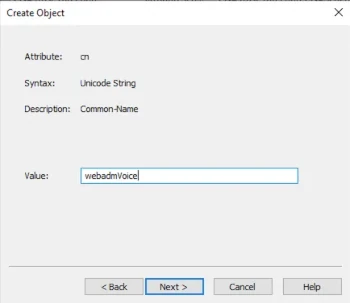
dn: CN=webadmVoice
changetype: add
attributeID: 1.3.6.1.4.1.34617.2.3.4
attributeSyntax: 2.5.5.10
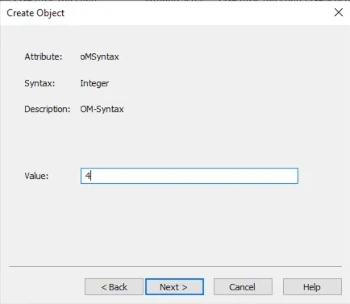
oMSyntax: 4
cn: webadmVoice
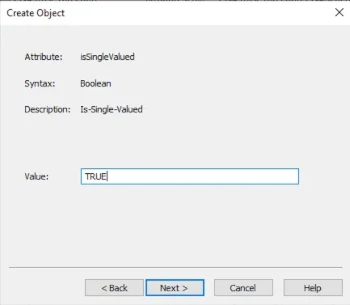
isSingleValued: TRUE
objectClass: attributeSchema
searchFlags: 0
All schema files are available in /opt/webadm/lib/schemas/ folder.
Have a look at section 5 of this documentation to manually update your AD schema.
5.1.2 Active Directory schema not extended
A new LDAP attribute which is commented out by default has been added :
If you want to use Voice biometric for authentication, you need to uncomment this setting.
#webadm_voice_attrs "audio"
5.2 servers.xml
As you can see, push and license configurations have been removed from your servers.xml file. The following content is now visible :
<!--
Removed Push Server Configuration Section
Replaced by Cloud services in WebADM v2.0
-->
<!--
Removed Push Server Configuration Section
Replaced by Cloud services in WebADM v2.0
-->
<!--
Uncomment the following block if you have a license server
with an IP pool-based Enterprise license from RCDevs.
-->
<!--
Removed License Server Configuration Section
Replaced by Cloud services in WebADM v2.0
-->
6. Update AD extended schema with webadmVoice attribute (optionnal)
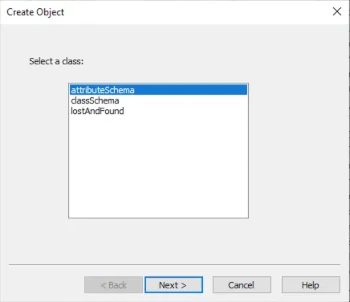
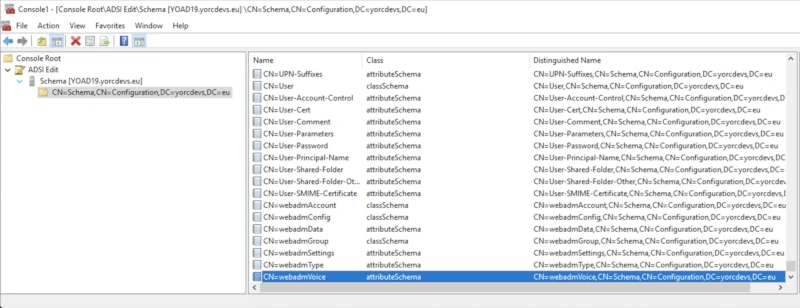
Open the AD schema snap-in on your domain controller which is schema master.
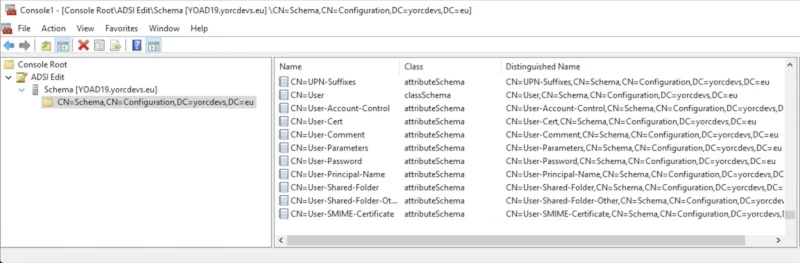
Right-click on the CN=Schema,CN=Configuration… object > New > Object.
And configure the new attribute like below :
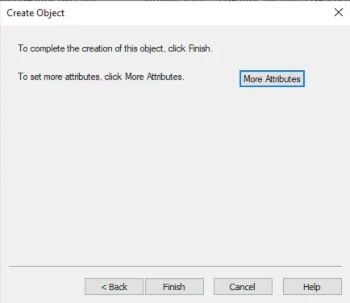
Click on the finish button. The new webadmVoice attribute has been added to your schema and should be available in the attributes list.
Edit the webadmVoice attribute > attribute editor. Found the searchFlag attribute and put 0 as value.
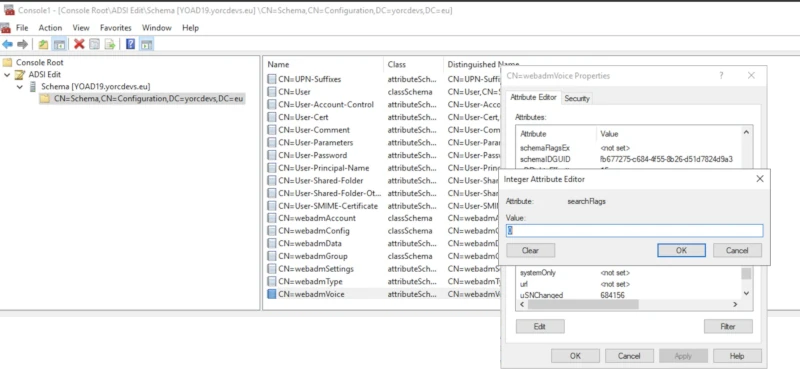
Save and exit.
Now, edit webadmAccount object and in attribute editor tab, edit the attribute mayContain:
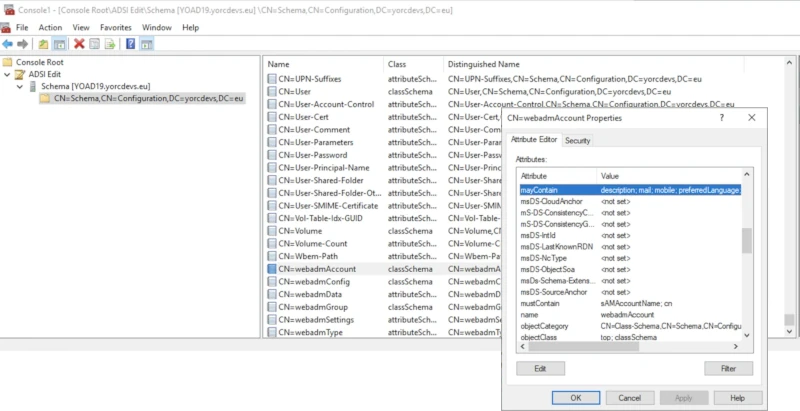
Add webadmVoice value
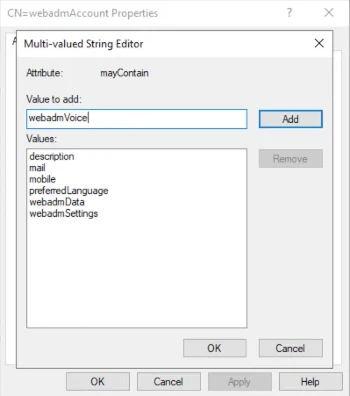
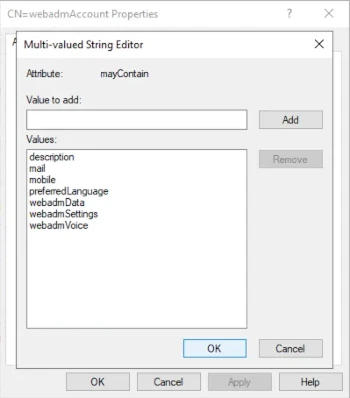
and save your changes.
Update your schema now :
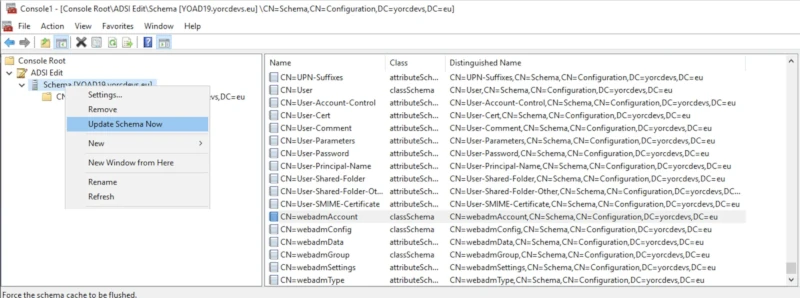
Schema extension is done, you should be able to register your Voice fingerprint in this new attribute.